Critical Palo Alto firewall vulnerabilities identified
Palo Alto Firewall Vulnerabilities Overview
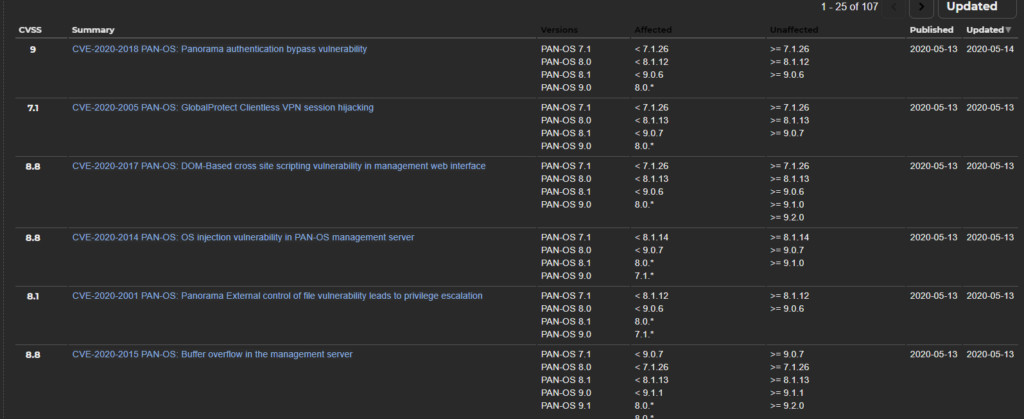
This threat report is about a series of critical Palo Alto firewall vulnerabilities that affect elements of the software suite. The major vulnerabilities are referred to as the following with varying degrees of severity: PAN-SA-2020-0005 PAN-OS, PAN-SA-2020-0006 PAN-OS, CVE-2020-2018, and CVE-2020-2005.
These vulnerabilities affect either the PAN-OS, Panorama, or the virtual private networking on the firewall. It seems like most of these software flaws have been fixed thus far, but they may pose a threat to your environment depending on the software versions. You can find a list of the most recently updated Palo Alto-related vulnerabilities linked below.
Tactics, Techniques, and Procedures Used
The Panorama function within Palo Alto is utilized to perform network security management of the environment. Panorama can be deployed physically, as a virtual appliance, or within a public cloud environment. Palo Alto firewalls in conjunction with Panorama can allow for network security policy and automated threat management.
The PAN-OS component of these next-generation firewalls is built to identity applications, users, and to perform content management. This component is designed to quickly identify and solve problems. The OS segment is the most important part of the overall network security architecture.
What These PAN-OS, Panorama, and VPN Vulnerabilities Mean to You
The exploitation of these vulnerabilities could affect your organization in the following ways:
- May lead to the loss of sensitive financial information.
- Could allow for a bad actor to pivot into the network.
- Acts as an excellent foothold for bad actors.
What You Should Do
It is highly encouraged that you implement upgrades to your network security architecture and consider running PAN-OS version 9.1. Consider implementing the patches linked below for more information.
Additional Resources
Security Advisories and Vulnerabilities:
- PAN-SA-2020-0005: https://security.paloaltonetworks.com/PAN-SA-2020-0005
- PAN-SA-2020-0006: https://security.paloaltonetworks.com/PAN-SA-2020-0006
- CVE-2020-2018: https://security.paloaltonetworks.com/CVE-2020-2018
- CVE-2020-2005: https://security.paloaltonetworks.com/CVE-2020-2005
Supporting Documentation:
- MITRE Mapping(s):
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.
Contact us for more information about Avertium’s managed security service capabilities.

Deciding between running an in-house SOC vs. using managed security services to add more rigor, more relevance, and more responsiveness to your cybersecurity program? Compare the two options. Download the e-book!