SonicWall Vulnerability may allow denial of service attack
This threat report is about a critical SonicWall vulnerability tracked as CVE-2020-5135 and includes actionable intelligence to mitigate damage.
SonicWall Vulnerability Overview
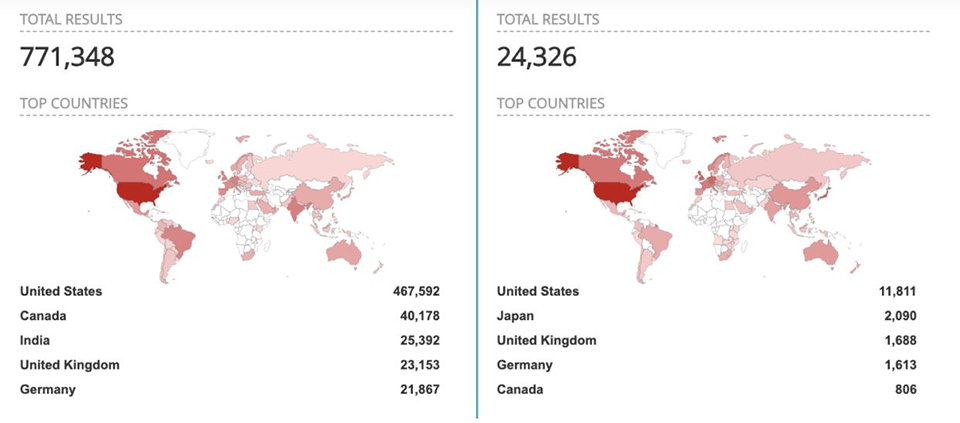
Exploitation allows a remote attacker to cause a Denial of Service (DoS) state and potentially execute arbitrary code on vulnerable systems. Shodan reveals approximately 800,000 VPN devices potentially running vulnerable SonicOS software. Companies running the listed versions should upgrade immediately because of the immense attack surface accessible via CVE-2020-5135.
Related Reading: Why Pen Tests are Key to a Robust Incident Response Plan
CVE-2020-5135 Tactics, Techniques, and Procedures
CVE-2020-5135 is a critical SonicWall VPN Portal stack-based buffer overflow vulnerability in SonicWall’s Network Security Appliance. The weakness resides within the HTTP/HTTPS service as well as SSL VPN remote access. This could be exploited by a remote, unauthenticated attacker by sending a specially crafted HTTP request with a custom protocol handler to a vulnerable device.
Successful exploitation of this vulnerability would result in a Denial of Service condition on the target. Researchers at Tripwire VERT have also confirmed the ability to “divert execution flow through stack corruption”, implying the presence of a remote code execution exploits also present in this vulnerability. CVE-2020-5135 exists pre-authentication and within SSL VPN which is typically exposed to the public internet.
Related Reading: Vulnerability Management: Is In-Sourcing or Outsourcing Right for You?
Based on searches run by Tenable, Shodan shows nearly 800,000 total VPN devices running potentially vulnerable SonicOS versions.
The identified vulnerable software versions and the associated fixed versions are listed below. Companies running any of the affected product versions are highly encouraged to update immediately due to the security risks presented by this vulnerability.
| Affected Versions | Fixed Versions |
| SonicOS 6.5.4.7-79n and below | SonicOS 6.5.4.7-83n |
| SonicOS 6.5.1.11 and below | SonicOS 6.5.1.12-1n |
| SonicOS 6.0.5.3-93o and below | SonicOS 6.0.5.3-94o |
| SonicOSv 6.5.4.4-44v-21-794 and below | SonicOS 6.5.4.v-21s-987 |
| SonicOS 7.0.0.0-1 | SonicOS 7.0.0.0-2 and above |
What This Means to You
- Exploitation will lead to loss of connection to network resources.
- Exploitation may lead to unauthorized access and control of company assets.
- Could lead to exceptional company production downtime.
- Could potentially lead to the exfiltration of sensitive company data.
What You Can Do
If your company uses one of the affected SonicOS versions, we recommend verifying that you are using the latest version available to remediate this threat in your environment. SSL VPN portals may also be disabled temporarily as a short-term mitigation action until the patch has been applied.
MITRE ATT&CK Techniques:
Sources
Need a company that will give you the expert advice about mitigating threats that you need to keep your business running smoothly? Read a comparison of in-house vs. outsourcing managed security services, download this free report.
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.