PrintNightmare – Unpatched remote code execution vulnerability in default windows print spooler service
Overview Details:
The PrintNightmare scenario continues to unfold as security researchers around the globe work to better understand how to detect and mitigate this critical vulnerability. The current best course of action is still to disable the Print Spooler service on all systems, however, there are business cases where printing is necessary, and disabling this service is not possible. Security researchers at TrueSec have developed a potential workaround to protect systems where print functionality is critical. They provide a PowerShell script to restrict access to the Windows print drivers directory by the SYSTEM account. This is effective in preventing the exploit, however, there have been reports that this can still cause problems with printing functionality, so please exercise extreme caution when deploying this script. A second PowerShell script is provided to roll back the changes should any problems occur.
There has been some confusion in the security community around whether PrintNightmare is the same vulnerability as CVE-2021-1675, which also affects the Print Spooler service. Current wisdom indicates that CVE-2021-1675 was a privilege escalation vulnerability that was in fact resolved by the June 8th Windows update, and PrintNightmare is a brand new zero-day exploit involving privilege escalation and remote code execution by a different method. It is unclear whether Microsoft will roll the new vulnerability into the existing CVE or generate a new CVE specifically for PrintNightmare. The severity of the issue and Avertium’s recommendations remain unchanged.
Affected Versions:
- Windows Server 2019
- Windows Server 2016
- Windows Server 2012
- Windows Server 2008
- Windows 10
Guidance:
- The June 8th Microsoft patch does not mitigate this vulnerability
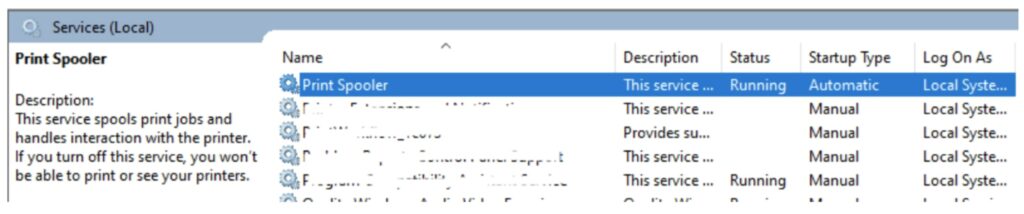
- Stop and disable the Print Spooler service on all Windows systems that are not involved in printer operations, especially Domain Controllers and Critical Servers
- Contact your Avertium SDM if you need professional services assistance disabling the Print Spooler service via GPO
- Use the ACL workaround developed by TrueSec on systems where printing cannot be disabled. Use extreme caution when deploying this script as there have been reports that it can still impact printing functionality. Use the provided rollback script if necessary
How Avertium is Protecting Our Customers:
- Avertium is performing threat hunts on SIEM and EDR platforms for known IOCs related to the published exploit
- Avertium has globally disabled the Print Spooler service on all internal Windows systems pending the release of a Microsoft patch to address the issue
References:
- https://blog.truesec.com/2021/06/30/fix-for-printnightmare-cve-2021-1675-exploit-to-keep-your-print-servers-running-while-a-patch-is-not-available/
- https://www.huntress.com/blog/critical-vulnerability-printnightmare-exposes-windows-servers-to-remote-code-execution
- https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2021-1675
- https://twitter.com/wdormann/status/1410198834970599425
- https://github.com/afwu/PrintNightmare
- https://www.tenable.com/blog/cve-2021-1675-proof-of-concept-leaked-for-critical-windows-print-spooler-vulnerability
- https://www.bleepingcomputer.com/news/security/public-windows-printnightmare-0-day-exploit-allows-domain-takeover/
- https://twitter.com/MalwareJake/status/1410421445608476679/photo/1
Contact us for more information about Avertium’s managed security service capabilities.