Palo Alto Firewall vulnerabilities discovered and patched
Palo Alto Firewall Vulnerabilities Overview
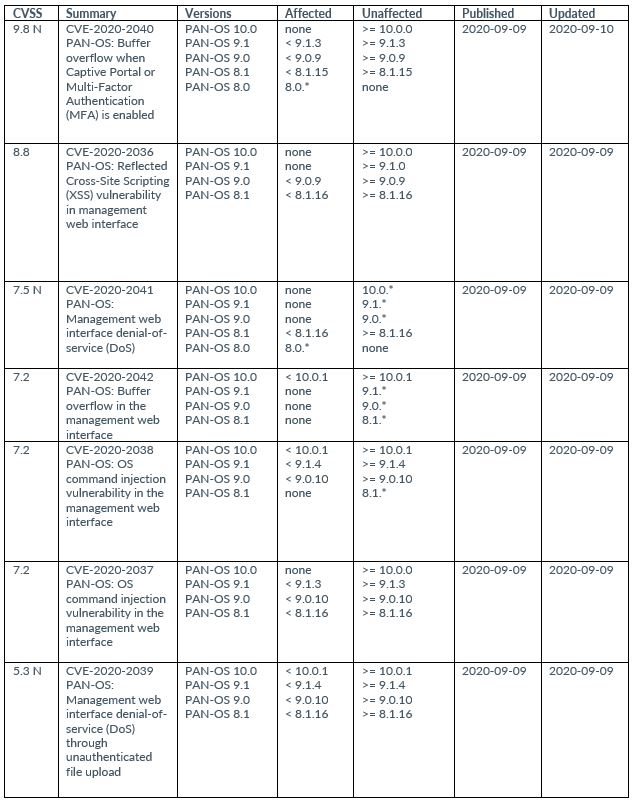
This threat report provides actionable intelligence about a series of vulnerabilities ranging in criticality affecting the Palo Alto firewall software suite. The vulnerabilities have been assigned the following CVEs (Common Vulnerabilities and Exposures) varies: CVE-2020-2036, CVE-2020-2037, CVE-2020-2038, CVE-2020-2039, CVE-2020-2040, CVE-2020-2041, CVE-2020-2042, CVE-2020-2043, and CVE-2020-2044.
The risk associated with these Palo Alto firewall vulnerabilities varies. These weaknesses either affect the web interface management, Captive Portal or Multi-Factor Authentication interface or the management interface.
Related Reading: Palo Alto PAN-OS Vulnerability with CVSS Score of 10 Issued
Tactics, Techniques, and Procedures
The most critical of the vulnerabilities is CVE-2020-2040 which may allow an unauthenticated attacker the opportunity to derail system processes and execute code using the root account. Successful exploitation is achieved by sending a specially crafted request to the assigned interface for the Captive Portal or for Multi-Factor Authentication. CVE-2020-2040 affects any Palo Alto firewall running any version of PAN-OS 8.0.
The vulnerability does not affect the GlobalProtect VPN or the PAN-OS management web interfaces.
Related Reading: Critical Palo Alto Firewall Vulnerabilities Identified
Below is a list of the vulnerabilities and a short description of them:
What This Means to You
- May lead to the successful compromise of a key infrastructure component.
- Could allow for lateral movement opportunities for a bad actor.
- May result in unwanted firewall changes.
What You Can Do
It is highly encouraged that you update to the latest version of PAN-OS to avoid the successful exploitation of these vulnerabilities.
Sources and Other Helpful Information
MITRE Mapping(s)
- https://attack.mitre.org/techniques/T1498/
- https://capec.mitre.org/data/definitions/88.html
- https://capec.mitre.org/data/definitions/591.html
- https://capec.mitre.org/data/definitions/100.html
Additional Resources
- https://security.paloaltonetworks.com/?severity=CRITICAL&severity=HIGH&severity=MEDIUM&product=PAN-OS&sort=-date
- https://security.paloaltonetworks.com/CVE-2020-2036
- https://security.paloaltonetworks.com/CVE-2020-2037
- https://security.paloaltonetworks.com/CVE-2020-2038
- https://security.paloaltonetworks.com/CVE-2020-2039
- https://security.paloaltonetworks.com/CVE-2020-2040
- https://security.paloaltonetworks.com/CVE-2020-2041
- https://security.paloaltonetworks.com/CVE-2020-2042
- https://security.paloaltonetworks.com/CVE-2020-2043
- https://security.paloaltonetworks.com/CVE-2020-2044
Contact us for more information about Avertium’s managed security service capabilities.

8 Steps to Take if You've Been Breached
With the prevalence, severity, and sophistication of cybersecurity attacks growing by the day, businesses of all types and sizes are scrambling to protect themselves. This best practices guide takes you through the 8 essential steps to managing a data breach. Download now.
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.