Ragnar Locker Ransomware New Evasion Technique
Overview of Ragnar Locker Ransomware New Evasion Technique
This threat report is about the Ragnar Locker ransomware and a new defense evasion technique used by the unnamed threat actor behind it.
The group has appeared more active in recent months and has recently been seen installing virtual machines on devices to avoid detection of the ransomware.
The primary motivation behind the group appears to be monetary gain.
Ragnar Locker Ransomware's New Tactics, Techniques, and Procedures
Normally the first step toward infection by Ragnar Locker ransomware is exploiting exposed services like Remote Desktop protocol. Ragnar Locker is also known to use Managed Service Provider (MSP) software like ConnectWise and Kaseya to infect victims.
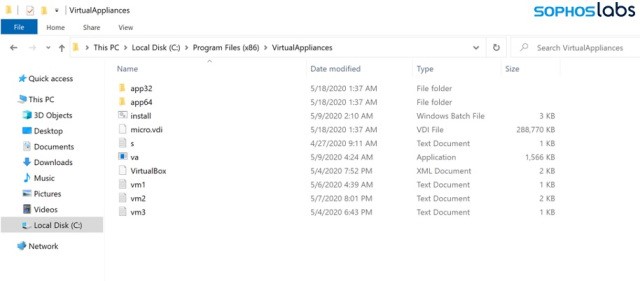
The initial attack vector may vary, but once initial access is gained, an MSI (Microsoft Installer) file is downloaded through PowerShell or Group Policy Objects. The file is executed to install Oracle VirtualBox, a Windows XP image to run, and files for executing commands on the host. These files are placed within the “C:\Program Files (x86)\Virtual Appliances” folder (see Figure 1).
Commands are then executed to perform a variety of tasks including stopping services, setting up the virtual machine, and removing shadow copies. VirtualBox is run in headless mode to avoid detection by anyone using the device.
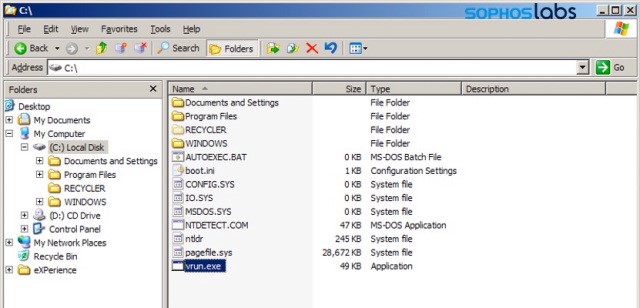
The virtual Windows XP machine runs the file “C:\vrun.exe” (see Figure 2) to mount the enumerated drives on the host operating system and encrypt them.
Following encryption, a ransom note is placed on the host operating system threatening to leak sensitive data if the ransom is not paid.
What This Means to Your Business
Ragnar Locker Ransomware infection can result in the following:
- Infection will lead to encryption or loss of data.
- Sensitive business data may be leaked to the public.
- Large payments have been demanded by the group of $500,000 or more.
- The true cost of ransomware infections can be in far excess of the demand due to a variety of factors like system downtime.
What You Can do to Protect Against Ragnar Locker's Detection Evasion Technique
We recommend the following steps to defend against infection by this malware:
- Update all software used for remote management of company assets with the most recently available patches. Follow general best practices on securing these tools.
- Enable PowerShell logging and ideally use a SIEM or similar tool to monitor for suspicious activity. Set the PowerShell execution policy appropriately on all devices to prevent suspicious scripts from running and allow only privileged users to run the program. Below are additional resources on this.
- Monitor use of hypervisor/virtualization software to detect suspicious virtual machines.
Additional Ragnar Locker Ransomware Information
Sources
- https://news.sophos.com/en-us/2020/05/21/ragnar-locker-ransomware-deploys-virtual-machine-to-dodge-security/
- https://www.bleepingcomputer.com/news/security/ragnar-locker-ransomware-targets-msp-enterprise-support-tools/
Supporting Documentation
- MITRE Mapping(s)
- Defense Evasion: https://attack.mitre.org/tactics/TA0005/
- Initial Access: https://attack.mitre.org/tactics/TA0001/
- External Remote Services: https://attack.mitre.org/techniques/T1133/
- Execution: https://attack.mitre.org/tactics/TA0002/
- Scripting: https://attack.mitre.org/techniques/T1064/
- PowerShell: https://attack.mitre.org/techniques/T1086/
Supporting links found through other resources.
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.
Contact us for more information about Avertium’s managed security service capabilities.

Deciding between running an in-house SOC vs. using managed security services (MSS) to add more rigor, more relevance, and more responsiveness to your cybersecurity program? Compare the two options. Download the e-book!