Government & Law Enforcement Crack Down On Cybercrime
GOVERNMENT INTERVENTION Executive Summary
In previous years, holding threat actors accountable for cyber attacks was difficult due to varying laws in different countries. These malicious individuals were able to cause significant damage to critical infrastructure across multiple countries, including the United States, without consequence. A great example of this is the December 2020 SolarWinds attack. Additionally, DarkSide’s cyber attack on Colonial Pipeline and REvil’s attack on Kaseya further proved the continued threat posed by cyber criminals.
However, over the past few years, governments and law enforcement in various countries have become more aggressive with taking down cyber criminals. Countries are starting to collaborate and take proactive measures toward stopping cybercriminal groups despite varying cybercrime laws. Within the past two years, large ransomware groups such as HIVE and the operators behind Emotet have been dismantled by law enforcement after several months or years of investigation. Let’s look at how law enforcement and government are changing their approach to cybercrime.
Government and law enforcement intervene and directly address cybercrime
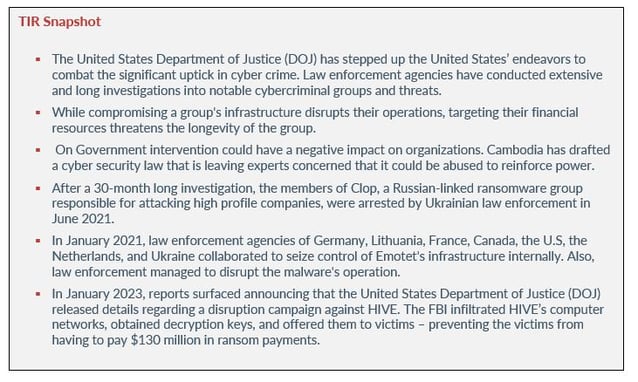
Law enforcement and government organizations have intensified their actions against cyber criminals by using a myriad of measures. The United States Department of Justice (DOJ) has stepped up the United States’ endeavors to combat the significant uptick in cyber crime. Law enforcement agencies have conducted extensive and long investigations into notable cybercriminal groups and threats.
The FBI has initiated operations against Ransomware-as-a-Service (RaaS) groups, causing some threat actors to vanish and then resurface after months or years (Clop, Emotet, HIVE, etc.). Certain nations, such as Australia, have urged other countries to act against cybercriminals who operate within their territories.
Law enforcement and governments across the globe are coming together to combat cybercrime. Threat actors such as HIVE didn’t expect for law enforcement to start hacking back, releasing decryptors, and saving organizations millions of dollars. While compromising a group's infrastructure disrupts their operations, targeting their financial resources threatens the longevity of the group. Although HIVE is still active and leaving digital breadcrumbs, it won’t be as easy as it was in previous years for the threat actors to breach organizations and keep their ransom payments.
Governments are also taking consequences a step further by sanctioning entire countries due to cyber attacks. In 2022, the Albanian government was attacked by HomeLand Justice twice. As a result of the attacks, the U.S. imposed sanctions on Iran’s Ministry of Intelligence and its minister for allegedly engaging in other cyber activities against the U.S. and its allies (Albania).
The U.S. government continued that thought process as they unveiled 2023’s Cyber Security Strategy from the White House, which includes:
- Abandoning the 2003 strategy which stated that federal regulation wouldn’t be a primary way of securing cyber space.
- The admission by the federal government of the inadequacy of voluntary cybersecurity standards highlights the need for regulatory mandates.
- The plan is for government agencies such as the Department of Defense (DOD), Securities and Exchange Commission (SEC), Federal Communications Commission (FCC), and others to use their authority to make sure all their contractors and suppliers follow specific cybersecurity rules that are required by law. If this is realized, it will help in the ability to detect and defend against cyberthreats.
GOVERNMENT INTERVENTION
On the flip side, government intervention could have a negative impact on organizations. Cambodia has drafted a cyber security law that is leaving experts concerned that it could be abused to reinforce power. Under the law, the government could take control of the computer systems and go through the data of companies that are unable to handle a major cyber attack. This law considers a cyber attack as a significant threat that could harm important aspects such as national security, defense, foreign relations, economy, public health, safety, or public order.
Oddly enough, Australia has a law with similar elements in their Security of Critical Infrastructure Act (SOCI). Australia’s law states that the Home Affairs Minister can require a critical infrastructure organization to take certain actions or abstain from doing something if a cyber security incident is severe. The organization must also accept help from the government, which can come in the form of "intervention requests" where the country's signals intelligence agency, the ASD, can take over some responsibilities. The legislation was controversial, but the government intervention came as a response to a severe ransomware attack where an impacted firm deliberately kept the government in the dark.
The security incident had a national impact on Australia and after two weeks, the government was only able to provide the firm with generic protection and advice. Three months after the original attack, the firm was reinfected. Based on Australia's experience, Cambodia's proposed law might seem like a good idea. However, what works in Australia might not be suitable for Cambodia. Australia's law has some safeguards, and there are independent groups that oversee it.
Cybersecurity can be complicated, but without rules, it's even more difficult to protect against attacks. When there are no mandatory requirements for cybersecurity, it becomes common to hear about security breaches happening frequently. Nonetheless, it is evident that governments and law enforcement agencies are taking measures to strike at cybercriminals where it hurts, by targeting their infrastructure, making arrests whenever possible, and recovering the profits they have unlawfully acquired.
CLOP RANSOMWARE GROUP
After a 30-month long investigation, the members of Clop, a Russian-linked ransomware group responsible for attacking high profile companies, were arrested by Ukrainian law enforcement in June 2021. The group posted around 15 leaks per month on their data leak page, and they were behind roughly $500 million in total financial damages.
In June 2021, law enforcement disrupted the ransomware gang and blocked channels for legalizing criminally acquired cryptocurrencies. They also conducted 21 searches in the capital, as well as in the Kyiv region. As news broke about the arrests, cyber criminals were nervously discussing the ordeal among their own networks via underground forums. Some started to see the group as being tainted and jumped ship. Clop was investigated for 30 months but that didn’t stop the group from continuing cyber criminal activity. However, the long investigation introduced a different era of cyber-criminal investigations and sent a message that cyber criminals are being carefully watched.
The Clop arrests focused on the supplier of the ransomware, but if law enforcement wants to truly keep track of ransomware and other cyber criminals, they will need to do more than take down large gangs. Law enforcement will need to also take down bottom feeders as it is not unusual for a ransomware gang to disband and join a smaller, lesser-known group to continue their mayhem. After the arrests, some of Clop’s infrastructure shutdown, however, that did not keep the ransomware gang from becoming active again. The group recently claimed attacks on 130 organizations by exploiting CVE-2023-0669 – a GoAnywhere zero-day vulnerability.
emotet MALWARE
Initially discovered in Europe in 2014, Emotet gradually expanded its reach and was responsible for numerous costly cyberattacks worldwide. The FBI launched its first investigation when a school district in North Carolina was compromised by the malware in 2017. Emotet has evolved incredibly since it was first observed and became increasingly stealthy in its ability to gain access to devices. The FBI saw Emotet hit almost every sector within the U.S., severely paralyzing large businesses, school systems, government services, and non-profits.
In January 2021, law enforcement agencies of Germany, Lithuania, France, Canada, the U.S, the Netherlands, and Ukraine collaborated to seize control of Emotet's infrastructure internally. Consequently, the law enforcement managed to disrupt the malware's operation. According to Europol, Emotet's framework involved numerous servers spread across the globe, each having distinct roles to oversee the systems of compromised victims – to spread to new targets, to serve other criminal groups, and to reinforce the network's resiliency against takedown attempts.
Emotet’s disruption came after the FBI unveiled a cyber strategy that prioritized efforts to impose greater cost and risk to cyber criminals, counting on robust alliances across every industry and various countries. The operation that disrupted Emotet, attested to how the FBI leveraged its knowledge, expertise, and global reach to make a huge impact.
hive ransomware
HIVE is a ransomware group that targeted over 1,500 businesses and organizations across the globe, including numerous healthcare organizations. The group employed a RaaS model, where developers created ransomware and promoted it to other cyber criminals. HIVE’s affiliates used the ransomware to attack victims and earn a percentage of the gains. Hive encrypts and steals data, demanding a ransom for both the decryption key and the promise to not publish stolen data. Hive made a total of $100 million in ransom.
Image 1: HIVE Domain Seized by Law Enforcement
Source: Malwarebytes
In January 2023, reports surfaced announcing that the DOJ released details regarding a disruption campaign against HIVE. According to the DOJ, since late July 2022, the FBI infiltrated HIVE’s computer networks, obtained decryption keys, and offered them to victims – thus preventing the victims from having to pay $130 million in ransom payments. The FBI was able to provide over 300 decryption keys to the victims who were actively under attack and distributed over 1,000 additional decryption keys to prior HIVE victims.
Also, with help from the Netherlands National High Tech Crime Unit and German law enforcement, the FBI seized the servers and websites HIVE used to communicate with members, which interrupted their ability to attack and extort victims. Although authorities continue to investigate and identify the threat actors involved in the HIVE operation, the hunt is far from over. Rewards for Justice program of the U.S. is offering a maximum reward of $10 million for any information that can establish a connection between HIVE or any other cyber criminals, who target critical infrastructure within the U.S. or a foreign government.
oasis WORMHOLE EXPLOIT
The Wormhole cryptocurrency platform was compromised in February 2022, resulting in the theft of $322 million in Ether currency. On February 21, 2023, the High Court of England and Wales ordered oasis.app, a DeFi company, to "take all necessary steps that would result in the retrieval of certain assets involved with the wallet address associated with the Wormhole Exploit on the 2nd February 2022". The $225 million was 'recovered' by exploiting a previously unknown vulnerability.
Last year brought massive crypto thefts, with threat actors stealing hundreds of millions of dollars in cryptocurrency in cases like this one. This is likely one of the first times we have seen a court order a ‘hack back’ to recover stolen digital assets. Expect to see more of this type of activity in the future as victims have less options to recover their data or cryptocurrency.
conclusion
Government and law enforcement have taken a stance on cybercrime and are actively working to crack down on those who perpetrate these crimes. The DOJ indictments against three Chinese intelligence officers and a computer hacker from China on Monday in correlation with an illegal cyber operation that took trade secrets and confidential data from numerous companies, universities, and public bodies in the U.S. and 11 other nations between the years of 2011 and 2018.
Cybercrime is a serious threat that can have serious consequences and both government and law enforcement are taking the necessary steps to protect the public. However, it is also important to remember that prevention is better than cure and that it is important to take preventative measures to reduce the risk of becoming a victim of cybercrime. With the right education and awareness, individuals can play an important role in protecting themselves, their families, and their communities from cybercrime.
how avertium is protecting our customers
Because the cyber landscape is always changing, it is imperative to be aware of new cyber attack strategies and techniques. Avertium is here to keep you informed and to keep your organization safe. We recommend the following services for the best protection against ransomware attacks:
- Avertium offers Vulnerability Management to provide a deeper understanding and control over organizational information security risks. If your enterprise is facing challenges with the scope, resources, or skills required to implement a vulnerability management program with your team, outsourced solutions can help you bridge the gap.
- Fusion MXDR is the first MDR offering that fuse together all aspects of security operations into a living, breathing, threat-resistant XDR solution. By fusing insights from threat intelligence, security assessments, and vulnerability management into our MDR approach, Fusion MXDR offers a more informed, robust, and cost-effective approach to cybersecurity – one that is greater than the sum of its parts.
- Avertium offers Zero Trust Architecture, like AppGate, to stop malware lateral movement.
- It is also recommended by Avertium and the FBI that your business require multi-factor authentication (MFA) to remotely access networks.
- Implementing network segmentation and filtering network traffic to stop phishing emails from reaching victims is also helpful.
- Reach out to your Service Delivery Manager or Account Executive if you need assistance applying any of the above recommendations.
SUPPORTING DOCUMENTATION
US Charges 4 Chinese Nationals in Hacking Campaign (voanews.com)
Cambodia cybersecurity law draft surfaces ahead of election - Rest of World
Hive Ransomware Operation Shut Down by Law Enforcement - SecurityWeek
Ukraine arrests Clop ransomware gang members, seizes servers (bleepingcomputer.com)
Russian government continues crackdown on cybercriminals | CyberScoop
Oasis Exploits Its Own Wallet Software to Seize Crypto Stolen in Wormhole Hack (yahoo.com)
Law Enforcement Cracks Down, Threat Actors Disappear & Re-Emerge (avertium.com)
Clop ransomware claims it breached 130 orgs using GoAnywhere zero-day (bleepingcomputer.com)
An In-Depth Look at the Emotet Botnet (avertium.com)
Emotet Malware Disrupted — FBI
With the White House’s strategy, the key to improving cybersecurity is finally here | The Hill
Hacking the Hive: How It Can Help Businesses | Burr & Forman - JDSupra
Hive Ransomware Operation Shut Down by Law Enforcement - SecurityWeek
Cybercrime focus of Justice Department crackdown on global hackers (usatoday.com)
Australia demands Russia crack down on cyber criminals | undefined (tbsnews.net)
The DoJ Disruption of the Hive Ransomware Group Is a Short-Lived Win (darkreading.com)
U.S. Department of Justice Disrupts Hive Ransomware Variant | OPA | Department of Justice
Australia demands Russia crack down on cyber criminals | Reuters
Senators unveil legislation to crack down on cyber criminals | The Hill
APPENDIX II: Disclaimer
This document and its contents do not constitute, and are not a substitute for, legal advice. The outcome of a Security Risk Assessment should be utilized to ensure that diligent measures are taken to lower the risk of potential weaknesses be exploited to compromise data.
Although the Services and this report may provide data that Client can use in its compliance efforts, Client (not Avertium) is ultimately responsible for assessing and meeting Client's own compliance responsibilities. This report does not constitute a guarantee or assurance of Client's compliance with any law, regulation or standard.
COPYRIGHT: Copyright © Avertium, LLC and/or Avertium Tennessee, Inc. | All rights reserved.
