Russian Drovorub malware affects Linux Systems
Drovorub Malware Overview
This threat report is about the Drovorub malware, which has been attributed to the Russian military unit known as the GRU (Organization of the Main Intelligence Administration).
The malware affects Linux systems and utilizes a unique method of persistence within an infected host. The malware is a part of the intelligence operations of APT28 (Advanced Persistent Threat).
Drovorub Tactics, Techniques, and Procedures
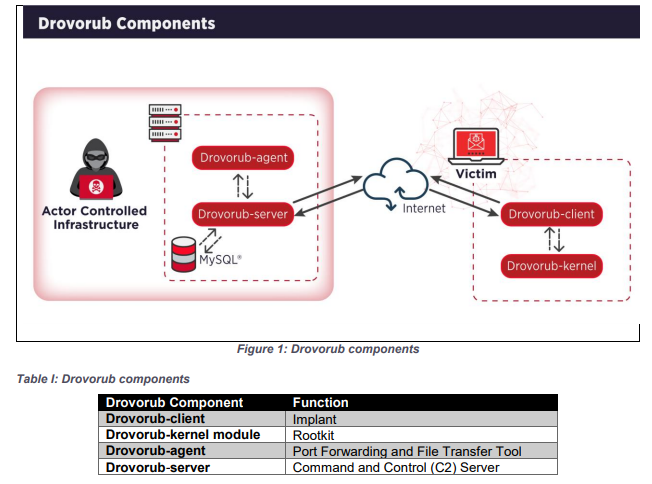
Drovorub malware operates as an installable agent on Linux hosts, performing a variety of reconnaissance operations on the network. The malware operates as a rootkit in conjunction with a toolset allowing for the ability to remain undetected. The client communicates with the command and control (C&C) server running a different version of the Drovorub software package.
Related Reading: Netwalker Ransomware Offered as Ransomware-as-a-Service Creating Increased Prevalence
Malware Components
Deploys Previously
Undisclosed Drovorub Malware
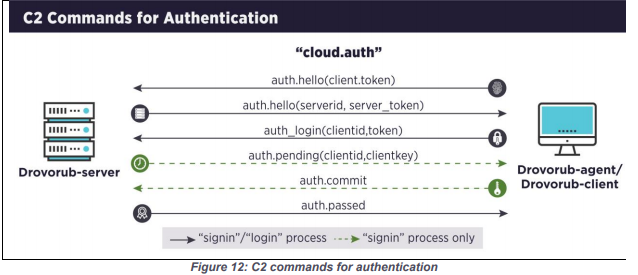
The Drovorub server maintains a mysql database of all the installed agents in the wild. The database manages the requests sent by the individual agents and handles the tasking process. The server authenticates each agent before issuing commands to the Drovorub agent.
The Drovorub client receives instructions from the server and starts the execution of those commands. The client can transfer files from the affected host or retrieve files from the command and control server. The agent can also port forward network traffic to hide its presence. It can open a remote shell for the bad actor as needed.
The client is packaged with a callback URL for the Drovorub server, a username/password for authenticating with the server, and an RSA public key for facilitating the authentication process with the server.
The kernel module is the rootkit element of this malware campaign. It hides the Drovorub malware’s activities from the administrator by not making the operations viewable to the userspace. It hides all the file manipulation and the network sessions created by the Drovorub malware. All the communication between the various components is done by JSON over WebSockets.
Authentication Model
Deploys Previously
Undisclosed Drovorub Malware
Related Reading: SIGRed “Wormable” DNS Server Vulnerability is Critical to Address
How Drovorub Affects You
- May lead to the loss of critical information and corporate secrets.
- May provide a foothold for a nation-state-level threat actor to perform reconnaissance operations on the network.
- May lead to the propagation of the malware on the affected asset.
What You Can Do about Drovorub
We recommend you perform the following actions on your critical assets running the Linux operating system:
- Limit the use of root account on the system.
- Use kernel protection tools like SELinux.
- Consider utilizing AppArmor to restrict the operations of the programs running on the system.
- Consider updating your Linux kernel to version 3.7 or later. This prevents unsigned kernel modules from loading on the system.
- Build Linux systems on hardware that supports and uses UEFI on x86-64 systems. Set your UEFI settings to either thorough or full mode.
- Install and scan your systems using either Rkhunter or Chrootkit.
- Harden your sysctl.conf file using the guide linked below.
Sources and Helpful Information
Source
MITRE Mapping(s)
- https://attack.mitre.org/techniques/T1090/
- https://attack.mitre.org/techniques/T1547/006/
- https://attack.mitre.org/techniques/T1544/
- https://attack.mitre.org/techniques/T1059/
Other Useful Information
- https://www.mcafee.com/blogs/other-blogs/mcafee-labs/on-drovorub-linux-kernel-security-best-practices/
- https://www.bleepingcomputer.com/news/security/nsa-discloses-new-russian-made-drovorub-malware-targeting-linux/
- https://otx.alienvault.com/pulse/5f3581cc4138be1d82c183b8
- Sysctl. conf hardening: https://www.cyberciti.biz/faq/linux-kernel-etcsysctl-conf-security-hardening/
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.
Contact us for more information about Avertium’s managed security service capabilities.
Deciding between running an in-house SOC vs. using managed security services (MSS) to add more rigor, more relevance, and more responsiveness to your cybersecurity program? Compare the two options. Download the e-book!