Achieve Secure Cloud Adoption using HITRUST
Most security teams are accustomed to operating in an environment where they have a high level of access to and control over their network infrastructure. In an on-premises data center, the organization owns and controls their own infrastructure, making it relatively easy to implement required security controls, perform audits, and achieve and maintain regulatory compliance.
When moving to the cloud, an organization transitions to a very different operating environment: The business leases infrastructure from a cloud service provider (CSP). As a result, the CSP and their customer share the responsibility for securing the organization’s network infrastructure, which creates challenges.
Challenges of Shared Responsibility
In a cloud deployment, the CSP provides their customers with full control over a certain layer of their infrastructure stack and little or no visibility or control under that layer. The point where this transition occurs depends on the service, whether it be Software-as-a-Service (SaaS), Infrastructure-as-a-Service (IaaS), or Platform-as-a-Service (PaaS).
With this shared control of infrastructure comes shared responsibility for security. Many CSPs publish a cloud shared responsibility model that delineates the duties assigned to each party and tools for clients to manage the aspects of security that are under their charge.
However, many organizations struggle with this shared responsibility model. In fact, only 27% of security professionals find shared responsibility models “very clear”, while 44.6% claim that they are “somewhat clear”, leaving more than a quarter (28.4 percent) who say that they are “not clear at all”.
HITRUST Simplifies Cloud Security
The HITRUST Cybersecurity Framework (CSF) is designed to provide a comprehensive and flexible guide for organizations attempting to achieve and maintain compliance with a number of regulations and standards.
As organizations increasingly embrace cloud computing, HITRUST has included guidance on how to ensure that cloud environments are secure. A critical part of this is understanding a CSP’s Shared Responsibility Model and verifying that an organization’s vendor is meeting compliance requirements as part of the auditing process, ensuring the entity is able to achieve secure cloud adoption.
HITRUST Shared Responsibility Matrix
HITRUST has created a Shared Responsibility Matrix to solve the challenge of organizations needing to be able to speak a common language around cloud supply chain risk to achieve secure cloud adoption. This will help all parties involved to agree on how to parse out control responsibility and inheritance between tenants and their CSPs with confidence that items will not fall through the cracks.
The Shared Responsibility Matrix assigns responsibility for the various security controls outlined in the latest version of the HITRUST CSF to the CSP or tenant. This helps to eliminate ambiguities in the Shared Responsibility Model that could result in a risk to an organization or finger-pointing after an incident has occurred.
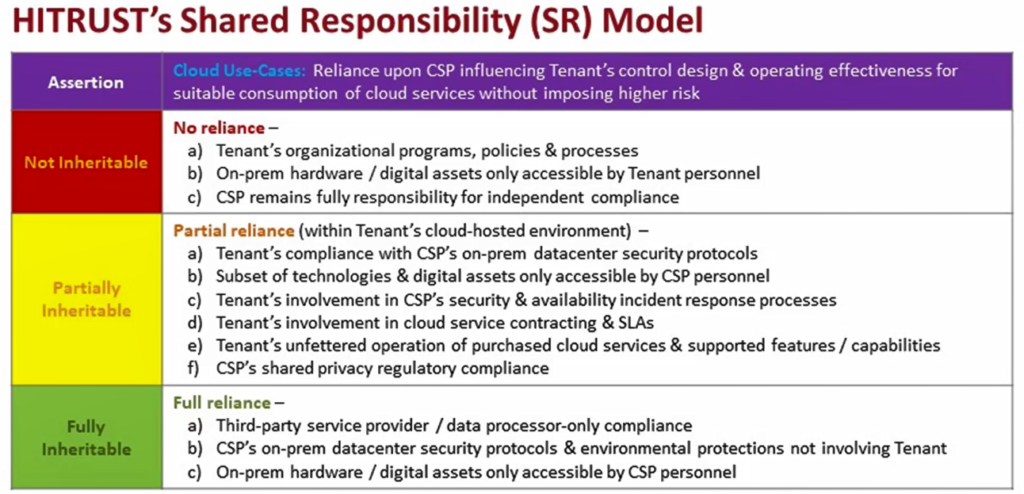
Figure 1. The HITRUST Shared Responsibility Model. Source: HITRUST Shared Responsibility Matrix Webinar
Figure 1 above provides a high-level breakdown of an organization’s security responsibilities based on how reliant an organization is on its CSP to achieve compliance.
The three levels of reliance are:
- Not Inheritable: The customer is completely responsible for managing security controls in this category
- Partially Inheritable: The customer relies partially on their CSP in order to implement these security controls
- Fully Inheritable: Responsibility for implementing security controls lies completely with the CSP
In general, the not inheritable and fully inheritable sections are easily identifiable. Customer is responsible for their internal security policies and procedures, and they can hold not responsible for ensuring the security of systems in the CSP’s environment that they have no access to or control over.
The partially inheritable section is where the HITRUST Shared Responsibility Model is extremely valuable. The full program, which is available as a free download as part of the HITRUST CSF version 9.3 download package, assigns each of the security controls from the HITRUST CSF to either the cloud customer or the CSP.
Downloading and working through this model removes a great deal of ambiguity regarding the cloud shared responsibility model and security and compliance responsibilities in the cloud.
Getting Started with the HITRUST Shared Responsibility Matrix
As new data protection regulations are enacted and go into effect, achieving and maintaining compliance is increasingly difficult. The HITRUST CSF is designed to help with this by providing a flexible and configurable framework of security controls designed to meet the data protection requirements of all regulations listed within the framework.
If you need help understanding how to use HITRUST CSF to ensure secure cloud adoption, or configuring it to match your organization’s regulatory requirements and unique environment, reach out for a consultation.