Introducing Norton 360 and Avira's Built-In Cryptocurrency Miners
Executive Summary
Almost everyone who owns a computer is familiar with antivirus software like Norton 360 and Avira. These products help customers protect their devices from malicious software like adware, worms, and trojans. For years, Norton 360 and Avira have been consistent with sticking to what they’re known for – antivirus software protection. However, recently these products have decided to take a step outside of their familiar services and offer their customers cryptocurrency mining services via their antivirus software. Why would Norton 360 and Avira offer this feature within their antivirus software? The answer may be more complicated than you think. Let’s dig into how the cryptocurrency mining program works and why consumers should exercise caution.
what is cryptocurrency mining?
Introduced in 2009, Cryptocurrency mining is just like mining for gold, diamonds, or other valuable materials. Instead of buying cryptocurrency (Bitcoin, Monero, Bytecoin, etc.), people can set up their computers at home to mine crypto tokens without having any capital. Despite being associated with cyber criminals, the act of cryptocurrency mining itself isn’t a crime. In fact, there are thousands of people who make a decent living from mining for cryptocurrency.
How Does it Work?
Various cryptocurrencies, such as Bitcoin, use distributed public ledgers to record all financial transactions. The transactions are public and each one is linked to the previous and subsequent transactions. Because those transactions are public, each record must be validated to prevent fraud. The validation includes solving a complex mathematical problem that is easy to verify. Cryptominers (a network of computers) compete to see who can solve the problem first. The miner (computer) that succeeds first is given the right to post the transaction to the ledger and receive a financial reward, which is paid in cryptocurrency.
Any computer can become a miner; however, the energy and hardware are quite expensive. Therefore, most people use cloud services to cryptomine. Cloud mining allows you to rent dedicated machines, also known as rigs. As a result, you can keep any cryptocurrency the rig mines.
norton 360 and avira's built-in cryptocurrency miners
During 2021, Norton 360 announced that they were including a built-in cryptocurrency mining program on their customers’ computers. Meaning, anyone who has the free Norton 360 ant-virus software on their computers received the cryptocurrency miner. A cloud-based service activates the cryptocurrency mining program and allows customers to profit. The program is “opt-in” which means that it will not be automatically enabled on customer computers, but instead a customer will have to manually enable the feature.
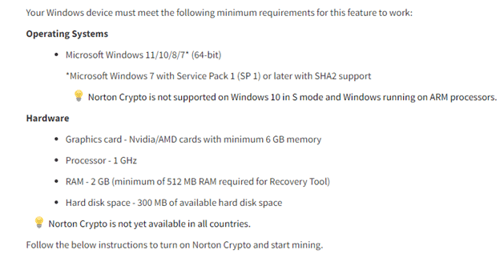
The built-in cryptocurrency miner is called Norton Crypto and mines cryptocurrency while your PC is idle. The miner was also allegedly installed without giving Norton’s current users notice. Norton Crypto mines Ethereum (ETH) cryptocurrency and only runs on systems that meet certain hardware and software requirements (like having a 1 GHz processor). Also, Norton creates a digital Ethereum wallet for customers where a key is encrypted and stored securely in the cloud. You can transfer the Ethereum from your digital wallet to Coinbase.
Image 1: Norton Crypto Device Requirements
Source: Norton.com
If you opt-in but decide later that you no longer wish to use Norton Crypto, you can disable the program. According to Norton 360’s FAQ page, the program is available in all Norton 360 plans where Norton determines that a computer meets the minimum system requirements. Right now, Norton Crypto is only supporting Ethereum crypto mining, but they are looking to add other currencies in the future.
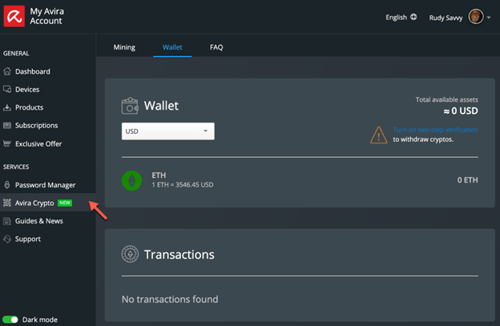
Avira Antivirus also introduced their users to cryptocurrency mining in 2021. Avira already has a built-in base of 500 million users due to their products being free. However, Avira was recently bought by the same company that owns Norton 360, NortonLifeLock Inc. Avira’s cryptocurrency miner is called Avira Crypto. Like Norton 360, Avira Crypto is automatically installed on every computer that runs Avira antivirus software, with customers opting in to use the service.
Avira’s FAQ page states that Avira Crypto uses your computer’s idle time to mine for ETH – the same as with Norton Crypto. Additionally, Avira Crypto allows you to disable the cryptocurrency mining program if you no longer wish to have it enabled. Your computer needs to meet the same system requirements as Norton Crypto in order to cryptomine and the miner is a free feature of all Avira security platforms. Avira Crypto has almost identical features to Norton Crypto, featuring a built-in personal wallet that allows you to transfer cryptocurrency to a Coinbase account.
Image 2: An Avira Cryptomining Account
Source: Avira.com
What's in it for Them?
According to Norton, Norton Crypto is included as a part of a free Norton 360 subscription. Avira Crypto is also a part of Avira’s free antivirus security software. Norton stated on their website that Norton Crypto is a way to help customers improve their cybersecurity by allowing them to mine cryptocurrency without having unvetted code on their devices that could be skimming their earnings or planting ransomware.
However, Avira and Norton made it clear in the FAQ sections on their websites that there are coin mining fees, as well as transaction fees to transfer your cryptocurrency. The coin mining fee is 15% of the crypto allocated to the miner and goes directly to Norton or Avira. This fact is interesting considering that cryptocurrency can be mined with regular mining software – which means you wouldn’t have to pay 15% to anyone. There are also transaction fees for transfers of cryptocurrencies which are paid to the users of the cryptocurrency blockchain network who process the transaction.
As we stated before, users who opt-in receive a digital wallet that allows them to store their earnings and then transfer them to Coinbase. However, several Norton Crypto users have taken to Norton’s online forum to address their troubles with withdrawals. According to the users, the transaction fees remain the same regardless of the amount of cryptocurrency being transferred therefore, the system is blocking withdrawals if the amount requested doesn’t cover the transfer fees.
the dangers for novice cryptocurrency miners
As with anything that has a financial reward, cryptocurrency mining comes with cautionary tales. Threat actors exploit cryptocurrency mining by using malware to mine on other peoples’ networks. This is called cryptojacking and can cause a network to become slower and less efficient – ultimately damaging the computer due to the level of work required to mine.
Because Norton Crypto and Avira Crypto are cloud based, there is a risk of threat actors gaining administrative access to those cloud environments and installing cryptomining malware. This malware has the potential to steal cryptocurrency, compromise sensitive data, and give attackers access to resources. Cryptomining involves pushing a device to its limit and can cause serious damage. The malware that’s installed uses a great amount of power and leaves computers running slow (or not running at all) and electricity bills soaring.
Threat actors like TeamTNT install cryptocurrency malware on vulnerable systems by performing mass internet scans. As one of the most active cybercriminal groups since mid-2020, TeamTNT has developed a sneaky tool kit for malicious activity. The tool kit includes Masscan and port scanner, librocesshider, 7z (decompresses files), b374k shell (controls infected systems), and Lazagne. This tool kit allows TeamTNT to go undetected even with the use of anti-virus and malware detection tools – making it difficult for cyber intelligence engineers and analysts to keep up with their activity. What’s stopping threat actors from scanning the internet for vulnerable devices and using Avira and Norton’s crypto mining programs as gateways? Nothing. Cybercriminals will always try to exploit new products.
Cyber security professionals are confused about the reasons why Norton 360 and Avira are exposing naïve consumers to the cryptocurrency world. Avira is a free product, and we can only assume that a lot of the people who use the product are not experts when it comes to cryptomining and the security concerns behind it. Cryptomining comes with its own set of security challenges therefore, exposing millions of less savvy internet users to a new (to them) part of the internet may do more harm than good in the long run.
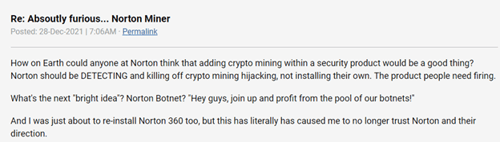
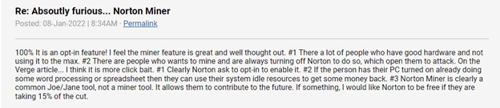
Additionally, members of Norton’s community forum are just as perplexed about the cryptomining feature. One user wants to know how adding cryptomining within a security product can be viewed as a “good thing”? The user went on to state that Norton should focus on detecting and derailing cryptomining hijacking, not installing their own.
Image 3: Norton Community Forum Comment
Source: Norton.com
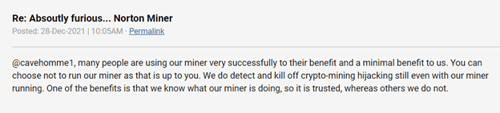
A Norton employee responded to the concerned user and assured them that the company is still killing off cryptomining hijacking even with the miner running.
Image 4: Norton Employee Response
Source: Norton.com
The issue that a lot of cyber security professionals and users are having is that the security of devices seems to be in question. We can see from Norton’s response that they are trying to reassure users that their devices will remain safe even with the miner running on their computers. It’s also important to keep in mind that the program will not run on your computer unless you manually opt-in. However, some users of Norton 360 and Avira don’t want the cryptomining program on their computer either way and were shocked to see that it was installed.
If you are interested in utilizing the feature, it’s important to remember that mining for cryptocurrency causes your computer to use more power, which can increase electricity costs and reduce the lifespan of your hardware. Security researcher, Chris Vickery, said that Norton 360’s cryptomining feature is only amplifying energy consumption and costing customers more in electricity than the customer makes doing the mining. Not all are opposed to Norton Crypto, including this forum member.
Image 5: Norton Community Forum Comment
Source: Norton.com
the future of cryptocurrency
Norton 360 and Avira aren’t the only ones trying to get in on the cryptocurrency wave. RadioShack believes they can bridge the gap and “cross the chasm” of mainstream usage for cryptocurrency because they are a very old brand. In 2020, they relaunched as an online-focused brand and now want to start their journey as a cryptocurrency exchange.
In December 2021, RadioShack announced RadioShack DeFi (short for decentralized finance), which is a market where people can trade newly announced RADIO tokens as an alternative to a centralized exchange like Coinbase. The details surrounding why the company thinks their consumers want to use cryptocurrency are murky, but the company’s website stated that they believe RadioShack is ready to lead the way for blockchain tech to mainstream adoption by other large brands. Their argument is that older customers don’t trust the new generation’s ideas surrounding cryptocurrency. RadioShack wants to focus more energy on making the “old school” consumer feel more comfortable due to the average “decision making” corporate CEO being 68 years old.
how avertium is protecting our customers
Cryptomining malware can disrupt your entire business operation and create a long-lasting impact. Affecting more than 55% of businesses worldwide, cryptomining malware is the No. 2 threat to consumers and businesses, with no signs of slowing down.
Norton’s and Avira’s antivirus software products are free for users. However, when security seems to be hanging in the balance, we recommend enterprise level antivirus protection like Avertium’s EDR services. Avertium offers the following services to keep your organization safe:
- Rather than point solutions, Avertium is able to fully integrate SIEM, EDR, Vulnerability Management, Zero-Trust Networking and Architecture & Integration Services, all by our certified experts 24/7. Avertium builds on customer relationships by creating, in collaboration with the customer, a methodical and disciplined forward motion by which to improve an organization’s security posture.
- Implement XDR as a prevention method. Our XDR is a combination of monitoring software like LogRhythm, Microsoft Azure Sentinel, or AlienVault, combined with endpoint protection such as SentinelOne. XDR platforms enable cybersecurity through a technology focus by collecting, correlating, and analyzing event data from any source on the network. This includes endpoints, applications, network devices, and user interactions.
- Avertium recommends utilizing our service for DFIR (Digital Forensics and Incident Response) to help you rapidly assess, contain, eradicate, and recover from a security incident like a cryptomining malware attack. This service is provided as an on-demand crisis response service, as well as retainer-based program.
avertium's recommendations
- Update your software with the latest security updates.
- Monitor traffic on your network. You should also monitor unreasonable bandwidth usage and outbound port scans.
- Use a well-configured firewall.
- You may want to limit the capabilities of specific IAM roles in the environment to reduce risk.
- Consider monitoring the environment for any odd outbound http requests containing sensitive AWS data.
- Educate your cyber intelligence team and your employees on the dangers of cryptomining malware.
- Use ad-blocking extensions – this can prevent malicious cryptomining code.
- Disable JavaScript – when surfing the web, disabling JavaScript can keep cryptojacking malware from infecting your computer.
MITRE TTPs:
- [T1589] Gather Victim Identity Information
- [T1609] Container Administration Command
- [T1610] Deploy Container
- [T1505] Server Software Component
- [T1555] Credentials from Password Stores
- [T1580] Cloud Infrastructure Discovery
- [T1496] Resource Hijacking
Indicators of Compromise (IoCs):
TeamTNT
- 8373c0e8abdd962f46d3808fb10589e4961e38cd96d68a4464d1811788a4f2b7
- 73a4e43a50c533dffdce6575a630be808780d1b408a6dda335106de0c48926ac
- 24c75a2f86d3c0f13f77b453d476787607a87c1033dca501351846524a4e8ff6
- e842c810b6ecb9c7634f1cfbf81b6245094528ac5584179eb8e6932eaa34f421
- 1e565e0672c4cd60b7db32c0ecc1abace6dfd8b6c2e0623c949d31536940fd62
- 12466d33f1d0e9114b4c20e14d51ca3e7e374b866c57adb6ba5dfef3ee34ee5b
- borg[.]wtf(45.9.150.36)
- Teamtnt[.]red(45.9.148.108)
- borg[.]wtf(123.245.9[.]147)
- anondns[.]net (13.245.9[.]147)
- 9.148[.]35/chimaera/bin/
- 9.148[.]35/chimaera/data/
- 9.148[.]35/chimaera/init/
- 9.148[.]35/chimaera/pl/
- 9.148[.]35/chimaera/py/
- 9.148[.]35/chimaera/sh/
- 9.148[.]35/chimaera/spread/
Domain Names for Cryptomining Pools
- F2pool – based in China and mines about 15% of all blocks.
- Poolin – based in China and mines 8% of all blocks.
- Binance Pool – owned by Malta-based exchange, Binance. Owns about 10% of all blocks.
- pool – Chinese based and accounts for 1% of all mining.
- com – public mining pool and mines about 7.5% of all blocks.
- Foundry USA – US based pool and accounts for 14% of all hashing power.
Supporting Documentation
TIR-20210913 TEAMTNT – “CHIMAERA” CRYPTOMINING MALWARE CAMPAIGN TARGETS SERVERS (avertium.com)
9 Best Bitcoin Mining Pools: Legit Sites (2022 Companies) (buybitcoinworldwide.com)
What is Antivirus Software | Webroot
Norton 360 Now Comes With a Cryptominer – Krebs on Security
What is Avira Crypto? – Official Avira Support | Knowledgebase & Customer Support | Avira
FAQ: Norton Crypto | Norton Community
Absolutely furious... Norton Miner | Norton Community
RadioShack is launching a crypto market for ‘the older generation’ - The Verge
Get started with Norton Crypto
Norton Crypto: Why an antivirus software company is now into cryptomining. (slate.com)
500M Avira Antivirus Users Introduced to Cryptomining – Krebs on Security
APPENDIX II: Disclaimer
This document and its contents do not constitute and are not a substitute for, legal advice. The outcome of a Security Risk Assessment should be utilized to ensure that diligent measures are taken to lower the risk of potential weaknesses be exploited to compromise data.
Although the Services and this report may provide data that Client can use in its compliance efforts, Client (not Avertium) is ultimately responsible for assessing and meeting Client's own compliance responsibilities. This report does not constitute a guarantee or assurance of the Client's compliance with any law, regulation, or standard.