Flash Notice: OpenSSL Project - Two High Severity Vulnerabilities
overview
Two critical vulnerabilities that were found in OpenSSL Project’s open-source cryptographic library have now been downgraded to high-severity. CVE-2022-3602 and CVE-2022-3786 affects OpenSSL version 3.0.0 and later. The flaws have been patched but could still be exploited by attackers.
CVE-2022-3602, an arbitrary 4-byte stack buffer overflow vulnerability, could trigger crashes or lead to remote code execution. CVE-2022-3786 is a vulnerability that could be exploited by attackers via malicious emails, allowing them to trigger a denial-of-service state via a buffer overflow.
OpenSSL stated that they are not aware of working exploits, and they did not have evidence of the vulnerabilities being exploited at the time of their advisory. The flaws have since been patched with the release OpenSSL 3.0.7 today. The patch comes on the heels of OpenSSL announcing that they would be releasing an update on November 1, 2022. According to Mark J. Cox, their policy is to provide people with a date for patches, then they will know to be ready to parse an advisory and see if the issue affects them.
“Given the number of changes in 3.0 and the lack of any other context information, such scouring is very highly unlikely.” – Mark J. Cox
However, the OpenSSL team stated that although the vulnerabilities have been downgraded, they still consider them to be serious. The reason why the vulnerabilities were downgraded from critical to high-severity is because they no longer believe the critical rating applied to CVE-2022-3602. OpenSSL’s policy states that “a vulnerability is rated critical if remote code execution is considered likely in common situations.”
CVE-2022-3602 was not rated critical from the beginning due to only the length and not the content of the overwrite being attacker controlled. OpenSSL 1.0.2, 1.1.1 and other earlier versions are not affected.
How Avertium is Protecting Our CUSTOMERS
- Avertium recommends utilizing our service for DFIR (Digital Forensics and Incident Response) to help you rapidly assess, contain, eradicate, and recover from a security incident like a malware attack.
- Fusion MXDR is the first MDR offering that fuses together all aspects of security operations into a living, breathing, threat-resistant XDR solution. By fusing insights from threat intelligence, security assessments, and vulnerability management into our MDR approach, Fusion MXDR offers a more informed, robust, and cost-effective approach to cybersecurity – one that is great than the sum of its parts.
- Avertium offers Vulnerability Management to provide a deeper understanding and control over organizational information security risks. If your enterprise is facing challenges with the scope, resources, or skills required to implement a vulnerability management program with your team, outsourced solutions can help you bridge the gap.
avertium's recommendations
OpenSSL Recommends the following:
- New applications should be developed to use the latest version of OpenSSL 3.0 (currently 3.0.7).
- Existing applications using OpenSSL 3.0 should upgrade to 3.0.7 as soon as possible.
- Existing applications using OpenSSL 1.1.1 are not affected by these issues.
- However, we always recommend using the latest version (1.1.1s). OpenSSL 1.1.1 is supported until 11th September 2023.
- Users of older versions of OpenSSL (such as 1.0.2) are encouraged to upgrade to OpenSSL 3.0.
- There was no release of OpenSSL 2.
INDICATORS OF COMPROMISE (IOCS):
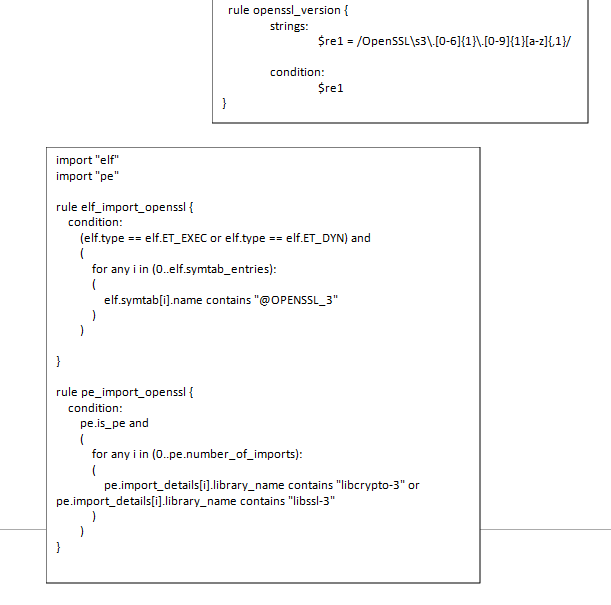
Yara Rules:
SUPPORTING DOCUMENTATION
https://twitter.com/iamamoose/status/1584908434855628800?s=20&t=7eVAek4eBgi_EifvgdxZIQ
CVE-2022-3786 and CVE-2022-3602: X.509 Email Address Buffer Overflows - OpenSSL Blog
OpenSSL fixes two high severity vulnerabilities, what you need to know (bleepingcomputer.com)
/news/vulnerabilities.html (openssl.org)
Effectively Preparing for the OpenSSL 3.x Vulnerability | Akamai