T-Mobile Data Breach Review: 40 Million Customers Compromised
On August 17th, 2021, T-Mobile was subject to a ransomware attack, which compromised over 40 million people’s private information. The information compromised came from customers, former customers, and prospective customers.
While customer financial information, such as credit and debit card information was not taken, the hacker, John Binns, (AKA screen names including IRDev and v0rtex) was able to take:
- SSN Numbers
- Names and Addresses
- Drivers License Numbers
- Dates of Birth
- IMEI (International Mobile Station Equipment Identity) and IMSI (International Mobile Subscriber Identity)Information
T-Mobile has “since identified an additional 667,000 accounts of former T- Mobile customers that were accessed with names, phone numbers, addresses and dates of birth compromised. These additional accounts did not have any SSNs or driver’s license/ID information compromised.” Additionally, the names of 52,000 people with Metro by T-Mobile accounts may also have been accessed, according to T-Mobile.
This wasn’t the first data breach within the telecom giant. The company has announced four data breaches over the last three years. T-Mobile disclosed a breach in January after incidents in August 2018, November 2019, and March 2020.
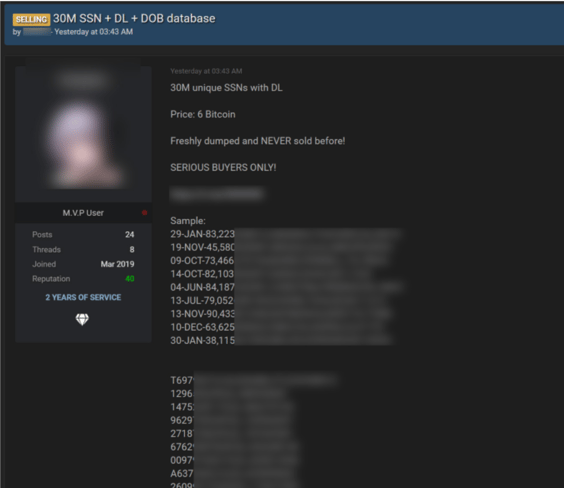 DarkWeb post of alleged T-Mobile Data for sale – C.O., Bleepingcomputer.com
DarkWeb post of alleged T-Mobile Data for sale – C.O., Bleepingcomputer.com
What Danger Does the T-Mobile Data Breach Pose to the Average Customer?
Identity theft relies heavily on Social Security Numbers, which, when combined with a driver's license (info also stolen), can be used to apply for everything from loans to credit cards.
Current T-Mobile clients could also be in jeopardy. Bad actors gained access to almost 8 million current users' account PINs. These pins are used to gain access to an account and the ability to alter and access personal information. Hackers using these PINs could obtain access to your phone number and use it for spoofing and other frauds. T-Mobile has a web page set up for suspected victims of this breach. It’s full of information from how they are protecting their customers, to what to do next. Please visit here for more information.
How was Binns Able to Breach T-Mobile’s System?
According to T-Mobile, “In simplest terms, the bad actor leveraged their knowledge of technical systems, along with specialized tools and capabilities, to gain access to our testing environments and then used brute force attacks and other methods to make their way into other IT servers that included customer data.”
Binns, who came forward as the hacker, stated that T-Mobile’s security was “awful.” Through unprotected routers and weak spots in T-Mobile’s internet addresses, Binns was able to gain access to over 100 servers. This took place on Aug. 4th and was reported by T-Mobile on Aug. 16th. (CNet)
What was the motivation behind the attack? Normally these are for financial gain, and ultimately this may end up that way. Reportedly, "This breach was done to retaliate against the US for the kidnapping and torture of John Erin Binns in Germany by CIA and Turkish intelligence agents in 2019," the threat actors told Alon Gal in a Twitter conversation. "We did it to harm US infrastructure." “It only took about a week, and generating noise was one goal,” Binns said, talking to the Wall Street Journal. One could only imagine he was trying to draw attention to inadequate security controls with the ease of penetration.
Ramifications and Recovery for T-Mobile Data Breach
Data breaches within any industry can have disastrous impacts upon the affected organization. RaaS gangs who infiltrate data systems are able to do more than cause financial suffering for a business as these breaches also influence brand reputation and customer relations.
-
T-Mobile Financial Loss
T-Mobile's stock continues to go down after the attack, along with now paying for new cybersecurity services, incident response plans, and McAfee’s Theft ID protection for 2 years for all customers affected. -
T-Mobile Will Invest in Expanding Cybersecurity Initiatives for Itself and Its Impacted Customers
They have now teamed up with cybersecurity firm Mandiant and consultants at KPMG in order to recover from this incident and protect themselves from future attacks. To ease customer tension, T-Mobile also now offers free identity theft protection, advanced spam-blocking, and access to its Account Takeover Protection service to protect postpaid customers from their phone numbers being stolen. -
T-Mobile's Loss of Customers & Third-Party Trust
Since the breach in T-Mobile's security, customers have begun to file class-action lawsuits against the company.
Below is a snapshot of the listed complaints filed in the class-action lawsuit recently filed against T-Mobile, citing neglect of proper cybersecurity and recommendations stating that the company only keep personal data for only as long as it is needed:
According to John Morgan and John Yanchunis, the Morgan & Morgan attorneys handling the case, "Consumers entrust their valuable, personal information to companies with the reasonable expectation that it be kept confidential and secure. T-Mobile, a leading telecommunications company, allegedly failed to fully implement a data security system to protect its customers from cyberattacks. Their alleged reckless actions and inactions have exposed customers to years of constant surveillance of their financial and personal records, monitoring, and loss of rights. We will continue to hold companies accountable and fight to ensure all institutions do more to protect people’s data.”
The Continued Exploitation of Organizations with Weak Cybersecurity
Large corporations continuously collect and store data from their customers, vendors, and third parties... moving their customers' data through IoT countless times. And unfortunately, with each transaction, come opportunities for Ransomware-as-a-Service (RaaS) gangs. Companies often fall victim to the illusion that "it won't happen to me" and will likely continue to ignore the possibility of a breach, exposing themselves to ransomware and the costs associated with recovering from an attack.
Attacks against companies like T-Mobile have become all too common in recent years:
- Verizon 2017 - “A contractor failed to secure a large batch of customer information, leading to data relating to 6 million customers' accounts being exposed.”
- Sprint 2019 - “Personal information was exposed to the darker corners of the internet. The hackers gained access via the Samsung ‘add a line’ website.”
- Mint Mobile 2021 - “A data breach occurred after an unauthorized person gained access to subscribers' account information and ported phone numbers to another carrier.”
How Corporations are Being Held Accountable for Breaches
There is no singular law at the national level that governs or protects the data of customers within large organizations, though there are specific rules and regulations which vary from state to state. (Read more: USA: Data Protection Laws and Regulations) This lack of definitive government guidelines on customer data gives a great deal of discretionary power to corporations and how they handle the personally identifiable information (PII) of their customers.
However, as these attacks become more frequent, the US government has begun to acknowledge the growing need for cybersecurity. President Biden recently issued an executive order that sets new regulations on cybersecurity for the public sector, which could signal incoming private-sector legislation in the near future.
Regardless of whether the government decides to impose mandates or penalties for companies with poor cybersecurity hygiene, the consumer culture around data protection is shifting, with nearly 80% of U.S. adults are “somewhat” or “very” concerned about how companies use their personal digital data (Pew Research Center). This shift in attitude could be even more effective in getting companies to take action.
In an entirely different lawsuit than the aforementioned class-action suit aimed at the most recent T-Mobile breach, the cellular providers T-Mobile, AT&T, and two other carriers currently face a proposed fine of $200,000 due to a lack of protection for customer information. AT&T is also currently facing allegations of a data breach, which they claim did not happen.
Related Reading: You’re Secure – But are Your Vendors? Assessing Third-Party Risk
Combating Raas Gangs and Data Theft
The growing need for cybersecurity requires Tactics, Techniques, and Procedures (TTP's) that are able to detect and eliminate potential threat actors before they reach your organization. For starters:
- Implement programs for ongoing vulnerability management, so your organization can effectively control your attack surface.
- Contain threats proactively by implementing ZTNA (Zero Trust Network Architecture)
- Think ahead about how to minimize the impact of a breach when it happens by enlisting a DFIR Service Provider (Digital Forensics and Incident Response). Getting a partner for this sooner rather than later can streamline the incident response process and contain the threat before it spreads, causing even more damage.