
Case Study:
INTERNOVA TRAVEL GROUP
Discover how Avertium helps unburden Internova Travel Group's security team to have the space to start focusing on more strategic cybersecurity priorities.
Since their emergence in 2019, the LockBit ransomware gang has become a highly infamous cyber gang. This group functions as a ransomware-as-a-service group that includes a core team responsible for creating the malware and overseeing its online presence and a large team of affiliates who carry out cyber attacks and earn a percentage of ransom payments.
The affiliates have been behind LockBit’s most major attacks including the attack on the German automotive giant, Continental, as well as the attack on the UK automotive giant, Pendragon. According to LockBit’s interesting list of affiliate rules, the percentage rate for their affiliate program is 20% of the ransom. Oddly enough, LockBit allows their affiliates to communicate directly with the companies they target and determine ransom demands. This means that affiliates can communicate however they please. Although LockBit is a large operation, their recent activity has led security researchers to believe that their empire may be slowly cracking. There is a lot of confusion surrounding what the group is doing and how their service is being managed.
Recently there have been suggestions that LockBit appears to claim victims without evidence. For example, the group claimed DarkTrace as a victim on their data leak site and implied that they stole the company’s data. However, when DarkTrace investigated, they found no evidence of a breach. It is now clear that LockBit made a mistake, confusing DarkTrace with threat intelligence company, DarkTracer who tweeted about the gang's leak site being filled with false victims. DarkTracer pointed out that LockBit's dependability seems to be diminishing and they have been careless in running their service, filling up their victim list with fake victims and insignificant data.
Avertium’s Cyber Response Unit (CRU) recently reviewed LockBit’s data leak website and found that some of the data exposed for a few companies was of little importance. Also, the website listed victims without corresponding data to go with them. This is consistent with LockBit investigations we have been involved in, where although the group may have had high levels of access to the victim environment, they were clumsy in their attempts to exfiltrate data and often failed to properly deploy their ransomware. Based on our observation, it is evident that the affiliates of LockBit’s operation are relatively unskilled.
However, despite these findings, LockBit remains the most prolific ransomware group by volume of attacks and are continuing to evolve their tools. In April 2023, security researchers discovered that a new version of LockBit ransomware has been targeting Apple’s Mac computers. Usually focusing on Windows and Linux machines, LockBit has a new build named “locker_Apple_M1_64.” It is highly possible that we may soon witness an upsurge in Mac ransomware infections, particularly if LockBit decides to make the Mac version of their ransomware available as a Ransomware-as-a-Service.
During 2022, LockBit was using an encryptor they named LockBit Black. The encryptor was challenging for security professionals due to each instance of the malware requiring a distinct password for successful execution. The password requirement made it very tough and sometimes impossible to analyze. Also, the malware employed a number of undocumented kernel-level Windows functions.
The CRU worked on a case that involved an organization being compromised by LockBit affiliates via the LockBit Black encryptor. During our investigation, we discovered that despite being a well-established and efficient operation, the affiliates deploying LockBit lacked sophistication. Let’s look at the tactics and techniques leveraged by LockBit’s affiliates and how subpar security can serve as an entry point for even the least sophisticated threat actors.
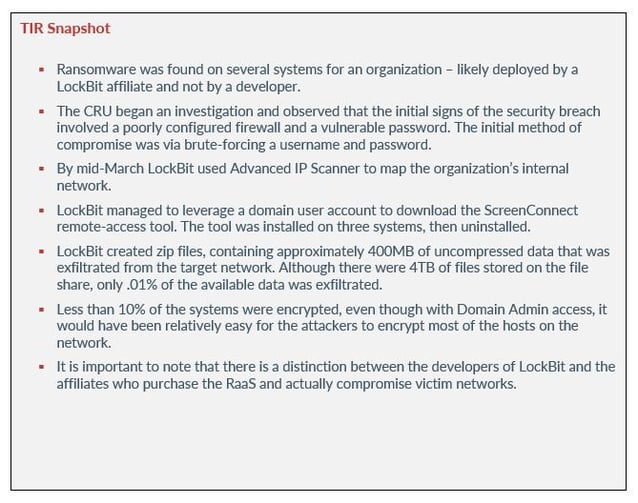
The victim organization reached out to Avertium after they found multiple indicators of compromise, including the presence of printed “LockBit Black” ransom notes on their internal printers. Following further investigation, ransomware was found on several systems.
The CRU began an investigation and observed that the initial signs of the security breach involved a poorly configured firewall and a vulnerable password. The initial method of compromise was via brute-forcing a username and password. We also found that the firewall had been misconfigured for nine days, and the system had default Windows event log settings that led to minimal records of login attempts. From the available logs it appears that within a matter of days of the firewall misconfiguration the victim IP was listed in Shodan, and multiple sources were actively launching brute force attacks. An account was compromised within seven days of the target system being exposed.
With access to an existing account, the threat actor was able to pivot to a domain account and create a new domain-administrator account with a different name. Using the new account, LockBit logged in via RDP to a Domain Controller before pivoting to and encrypting sixteen server systems.
Within two days of the initial compromise the threat actor used Advanced IP Scanner to map the organization’s internal network. The tool was used to gain a better understanding of the network's topology and identify potential vulnerabilities that could be exploited. By scanning the network, LockBit obtained information about hosts, services, and open ports.
After successfully mapping the target’s internal network, LockBit downloaded an executable named IOBitUnlocker.exe and used it to access files that were locked or in use. The tool is used to unlock multiple files or folders on desktops or other places at the same time.
Next, the ransomware group managed to leverage a domain user account to download the ScreenConnect remote-access tool. LockBit installed the tool on three systems, then uninstalled it before conducting further network mapping using Netscan.exe. The CRU did not find any evidence that ScreenConnect was used, and a full disk scan showed that it was installed on one of the domain controllers before it was removed.
The threat actor created zip files, containing approximately 400MB of uncompressed data that was exfiltrated from the target network. Although there were 4TB of files stored on the file share, only .01% of the available data was exfiltrated. To carry out the exfiltration, the attacker utilized the Rclone remote file synchronization utility to transfer the stolen data to api.put.io and premiumize.me. LockBit attempted to use ngrok as well, but that was unsuccessful due to detection and blocking at the firewall.
Despite limited firewall logging detail, there was unmistakable evidence of LockBit having accessed file storage internet sites. Forensic analysis also confirmed successful file uploads.
Four days after initial access the threat actor successfully encrypted sixteen server systems, involving multiple file types and filenames. However, it's worth noting that less than 10% of the systems were encrypted, even though with Domain Admin access, it would have been relatively easy for the attackers to encrypt most of the hosts on the network. It's also noteworthy that while the backup server itself was encrypted, the data repository was not, and therefore remained unencrypted. This evidence shows the inexperience of LockBit affiliates.
Strangely, Get-ADUser was used to collect user accounts from Active Directory after systems had been encrypted. Get-ADUser is a command in PowerShell that is used to retrieve information about Active Directory user accounts. Using the Get-ADUser command, threat actors can obtain information related to a user's account in Active Directory, including their name, email address, group memberships, account status, and other information. In most investigations encryption is the final action by the threat actor.
When it comes to the ransomware-as-a-service (RaaS) model, LockBit is often referred to as a "well-oiled machine." However, despite LockBit’s efficiency as ransomware, it appears that not all LockBit affiliates are particularly sophisticated or advanced. There is a difference between the developers of LockBit and the affiliates who purchase the RaaS.
In this case study, we can assume that we are dealing with LockBit affiliates and not developers based on several obvious mistakes. While the developers may not have the most advanced affiliates, their expertise lies in creating a platform that is easy to use and highly profitable for affiliates.
LockBit used several tools to carry out their attack, which include:
It should be noted that most of these tools are legitimate software and will not be detected as malware unless custom rules or application whitelisting is in use.
|
Filename |
SHA1 |
|
LBB.exe |
3dbeeed8320fb5c91394dfc0014984e25dc95732 |
|
5in_d.exe |
50f442ebbb1142db310f6b96f71afef4e49b320f |
|
LBB_ReflectiveDll_DllMian.dll |
b35ab076f864dd5570aff12d535ca5f5bcd2bf6c |
|
Jdwj.sys |
b6c4f2a7585f6ed77a55aa90de98307fc468b882 |
|
LBB_pass.exe |
c8db61274c4d102b88a38aadc967e12d1fcffebc |
|
LBB_Rundll32_pass.dll |
e4e2ffa1079faa55d2c0b7177829531feb78255e |
|
LBB_Rundll32.dll |
eeb9611bee1934145e82e8cc2249b7610840e664 |
Because the cyber landscape is always changing, it is imperative to be aware of new cyber attack strategies and techniques. Avertium is here to keep you informed and to keep your organization safe. We recommend the following services for the best protection against ransomware attacks:
Advanced IP Scanner: the preferred scanner in the A(P)T toolbox (huntandhackett.com)
ScreenConnect MSP Software Used to Install Zeppelin Ransomware (bleepingcomputer.com)
ScreenConnect - https://www.screenconnect.com/
LockBit affiliate behind major attacks arrested in Canada | Cybernews
Uncovering LockBit Black's Attack Chain and Anti-Forensic Activity (quickheal.com)
What is nssm.exe (The non-sucking service manager) used for? (file.info)
What is Remote Desktop Protocol? Using it! & Best RDP Alternatives 2023 (comparitech.com)
LockBit 3.0 Ransomware Unlocked - VMware Security Blog - VMware
Darktrace: Investigation found no evidence of LockBit breach (bleepingcomputer.com)
LockBit Ransomware Targets Apple Silicon Macs for the First Time | PCMag
Related Resource:
Note: Please be advised that the affiliate rules seen below were translated via Google Translator, therefore there may be errors.
The oldest international [Ransomware] LockBit affiliate program welcomes you.
We are located in the Netherlands, completely apolitical and only interested in money. We always have an unlimited amount of affiliates, enough space for all professionals. It does not matter what country you live in, what types of language you speak, what age you are, what religion you believe in, anyone on the planet can work with us at any time of the year.
First and foremost, we're looking for cohesive and experienced teams of pentestors. In the second turn we are ready to work with access providers: sale or on a percentage of redemption, but you have to trust us completely. We provide a completely transparent process - you can control the communication with the victim. In case when the company was encrypted and has not paid, you will see the stolen data in the blog.
We also work with those who don't encrypt networks, but just want to sell the stolen data, posting it on the largest blog on the planet. Brief description of functionality:
All this and much more awaits you, if you join our team. If you do not find one of your favorite features, please inform us, maybe we will add it especially for you.
Rules of the affiliate program:
Categories of targets to attack:
Every candidate to join our affiliate program should understand that we are constantly trying to be hacked and harmed in some way. This is why we pay a lot of attention to the candidates who join our partnership program. When joining, a lot of factors are taken into consideration, such as the reputation on the forums, the team composition, evidence of work with other affiliate programs, your wallet balance, the amount of previous payments and much more. You can also join our team by a guarantee of our partners, who are already active and time-tested.
After many years of experience, we concluded that the most effective way to test a candidate for accession is a deposit. When you join, you deposit 1 bitcoin in our wallet, in fact, this amount is an advance and will be used at your subsequent payments as payment for our 20% share. For example, the company paid you a ransom for decrypting 100 bitcoins, you have to transfer a share of 20 bitcoins to us, but thanks to the deposit you made when you joined, the amount of the share paid will be 19 bitcoins. This procedure is required only once, only when you join the affiliate program. The deposit weeds out insecure newbies, cops, FBI agents, journalists, white haters, web pentesters, competitors, and other small rodent pests.
The deposit amount may be reduced or not required at all, depending on what reputation you have and what information you can provide about yourself. For those who are afraid to trust us with their money and think that we are scammers, it is possible to carry out this procedure through a guarantor, any reputable forum, in this case, you make a deposit on the balance of the forum, where we describe the conditions of the deposit, which are very simple, for example, if you can not earn 5 bitcoins in a month, then your deposit goes to us.
Please, be understanding with such a careful attitude to your candidacy, because you personally would not be very pleased if your newly encrypted company was decrypted for free by the FBI thanks to some person who easily gained access to the panel and made a masterful hack of our servers using zero-day vulnerabilities.
Recommended, but not required, application form when joining:
1) Links to your profiles on various hacker forums - the older your account, the better.
2) Describe your experience with other affiliate programs, preferably with some evidence, such as screenshots and transactions that show your payouts.
3) Show your balance in cryptocurrency at the moment.
4) Explain the reasons why you left another affiliate program and want to work with us.
5) Tell about the current accesses you have and are ready to attack immediately after joining us. It is recommended to prove yourself immediately after joining - the sooner you get the first payment, the less doubt will be cast on your identity.
6) It is desirable to have already downloaded information for the blog from the intended target for the attack and provide evidence of the existence of this information, such as screenshots, file tree or access to these files.
7) Ask your friends or acquaintances who already work with us to vouch for you.
8) Request a bitcoin or monero wallet to make a deposit, in case you are confident in your abilities and ready to earn millions of dollars with us.
To summarize, the reasons why it is better to work with us:
This document and its contents do not constitute, and are not a substitute for, legal advice. The outcome of a Security Risk Assessment should be utilized to ensure that diligent measures are taken to lower the risk of potential weaknesses be exploited to compromise data.
Although the Services and this report may provide data that Client can use in its compliance efforts, Client (not Avertium) is ultimately responsible for assessing and meeting Client's own compliance responsibilities. This report does not constitute a guarantee or assurance of Client's compliance with any law, regulation or standard.
COPYRIGHT: Copyright © Avertium, LLC and/or Avertium Tennessee, Inc. | All rights reserved.