The Defined Approach:
Essentially, this is the same approach that has always been used in previous versions of PCI DSS. The only difference is that PCI 4.0 provides more clarification on the 64 stated requirements. The defined approach follows the traditional validation process outlined in PCI 4.0 and is best suited for healthcare organizations with defined controls in place, but also has a desire for more structure.
Some organizations taking the defined approach are expected to self-assess. The PCI DSS Self-Assessment Questionnaire (SAQ) is a validation tool intended to assist merchants and service providers in self-evaluating their compliance with the PCI DSS. Alternatively, if an organization is ineligible for self-assessment, a PCI QSA can come in to conduct defined testing procedures and help the organization meet the stated requirements in PCI 4.0. After the assessment is conducted, organizations must fill gaps where a requirement is not met.
The Customized Approach:
This is best suited for healthcare organizations that have developed a high level of maturity or sophistication in managing risks. It provides businesses with the flexibility to create their own distinct security measures to fulfill regulatory data security requirements.
According to Lauren Holloway, Director of Data Security Standards, “The customized approach is for entities that choose to meet the requirement differently than is stated. In this case, the entity must meet the stated Customized Approach Objective instead of the stated requirement. The customized approach is most successful when the entity has robust security processes and strong risk management practices and is able to effectively design, document, test, and maintain security controls to meet that objective.”
Organizations taking the customized approach are expected to have their PCI QSAs derive appropriate testing procedures to validate the implementation of the stated objectives in PCI DSS 4.0. This allows organizations to implement controls that fit their environment’s unique needs while taking into account the purpose of each objective.
The Clock is Ticking to Become PCI 4.0 Compliant
PCI DSS applies to a diverse range of industries, one of which is the healthcare sector. When most people think about the compliance frameworks that healthcare organizations need to meet, they think of HIPAA. While the Health Insurance Portability and Accountability Act (HIPAA) is typically associated with healthcare compliance, Payment Card Industry Data Security Standard (PCI DSS) is equally significant for healthcare entities that accept payment cards for services or goods.
In other words, merely being HIPAA compliant, which pertains to a distinct category of confidential information (individually identifiable health information), does not exempt healthcare entities from the obligation to protect each patient’s financial information as well.
Established almost two decades ago, the PCI DSS is a set of security guidelines designed to ensure that all entities that handle, store, or transmit cardholder data maintain a secure environment.
Recognizing the ever-changing landscape of e-commerce and the growing sophistication of cyber threats, PCI DSS constantly evolves to stay ahead of potential vulnerabilities. The most recent iteration of the standard, PCI 4.0, was unveiled in March 2022.
What is PCI 4.0?
Key Changes in PCI 4.0:
As the healthcare payment industry expands, it is time for us to acknowledge that a one-size-fits-all approach to compliance is no longer practical. PCI 4.0 brings forth 64 new requirements with options between the traditional, defined approach and a new, customized approach to compliance. Among those key changes include:
-
Implementing a more rigorous multi-factor authentication (MFA)
-
Cross-checking passwords against a list of known compromised and bad passwords to enhance password controls
-
Bolstering overall protection with new security standards related to e-commerce and phishing attacks
-
Assigning roles and responsibilities for each requirement and guidance to help people better understand how to implement and maintain security
For more information: Summary of Changes from PCI DSS
PCI 4.0’s customization approach aims to not only improve procedures for organizations using different methods to achieve their security goals, but also to increase flexibility.
Timeline for PCI 4.0 Implementation:
Since PCI 4.0’s release in March 2022, all healthcare organizations and applicable entities are given a transition period of two years, ending on March 31st, 2024.
During this time, PCI 3.2.1 is still in operation. From now until its retirement date, healthcare organizations will be able to choose which version (3.2.1 or 4.0) they use for assessments. Keep in mind that healthcare organizations must still meet the requirements of PCI 3.2.1 while familiarizing themselves with the changes in 4.0. This means updating report templates and planning / implementing changes to meet the new requirements.
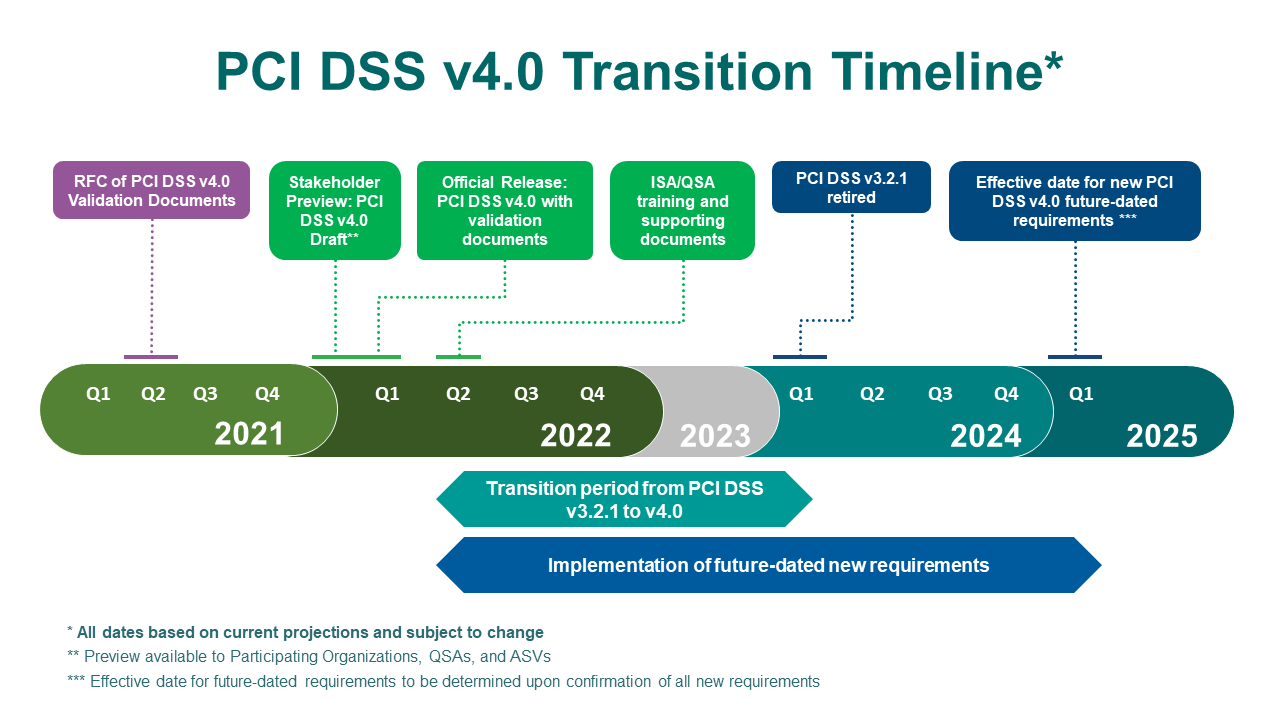
Source: PCI Security Standards
To ensure a successful implementation, the involvement of a PCI QSA (Qualified Security Assessor) is necessary. A PCI QSA is an individual employed by a QSAC (Qualified Security Assessor Company) and certified by the PCI Security Standards Council as a PCI compliance assessor. Engaging a QSA to assess potential security threats significantly reduces the risk of incurring fines or experiencing a costly security breach.
Who Does PCI 4.0 Apply to?
PCI 4.0 primarily applies to merchants. “Merchants,” in the healthcare sector, means any healthcare entity that accepts payments from 5 major credit card companies:
- American Express (Amex)
- Discover
- Japan Credit Bureau (JCB)
- MasterCard (MC)
- Visa
On the other hand, PCI 4.0 can also apply to service providers. These are business entities that offer services to other organizations that process, store, or transmit cardholder data such as:
It is important to keep in mind that a merchant can also be considered a service provider if they process, store, or transmit cardholder data for other merchants or service providers.
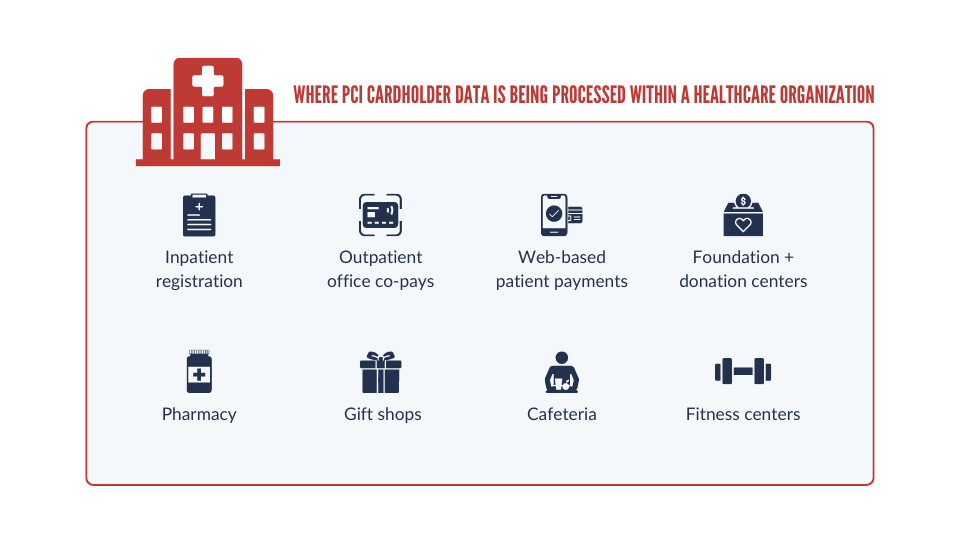
Within a healthcare organization, credit card payments are processed in a diverse range of settings, which are frequently overlooked in information security and compliance program models. By picturing where PCI cardholder data is being processed within a healthcare organization, you can better understand whether or not PCI 4.0 applies to your organization.
As a result, it is imperative that healthcare organizations – along with their third-party payment card processing providers – align their policies, procedures, and technical implementations with the updated requirements of PCI 4.0.
Related Resource: Overview of PCI Software Security Framework
PCI 4.0: Customization Capability Overview
One of the most significant changes in PCI 4.0 is that, now, organizations can take a more customized approach to meeting the PCI mandate. Because compliance requirements can vary depending on the industry, size of the organization, and geographic location, a customized approach allows for more flexibility that takes into account unique factors and needs within your organization.
Related Resource: Top 5 Threats in the Healthcare Industry
Customized PCI 4.0 Controls:
Organizations are expected to have their PCI QSA derive appropriate testing procedures to validate the implementation of the stated objectives in PCI DSS 4.0. This allows organizations to implement controls that fit their environment’s unique needs while taking into account the purpose of each objective.
Some examples of customized controls a PCI QSA can help organizations implement include:
-
Choosing the types of scans and the pace at which you do them:
The organization can perform a targeted risk analysis to determine the scan's frequency. -
Adding applicable security controls that are specific and needed to protect your environment:
Each environment is different, a company can use a new tool that offers better protection or maybe suits their environment better. -
Adding a system in place to check password integrity:
The organization can implement a password strength assessment mechanism to check the strength of passwords by utilizing libraries and algorithms that analyze passwords against common patterns, dictionary words, and known weak passwords. -
Documenting new behaviors in your security controls to keep them updated without the constant need to buy new technology:
Implementing EDR in the environment can help detect changes in endpoint behavior. By monitoring and analyzing endpoint activities, EDR solutions can detect suspicious processes, unauthorized system changes, or unusual network traffic, allowing security teams to proactively respond to potential threats.
Advantages of Customizing PCI 4.0:
-
Save money over the long term: PCI 4.0 can be implemented in-house with the help of an MSSP that has certified QSAs. By using this approach, you can reduce the number of tools being used and update to more specialized software needed to minimize budgetary concerns.
-
More flexibility in your technology infrastructure: With the added flexibility that PCI 4.0 offers, organizations can use whichever technologies they choose – whether that’s cutting-edge technology or your existing tech stack.
-
Increased efficiency: Using one action to fulfill multiple compliance frameworks can significantly enhance efficiency for organizations. Instead of implementing separate procedures and processes for each compliance framework, a customized compliance approach allows for the consolidation of effort, streamlining processes and avoiding unnecessary or redundant procedures. As a result, saving time and resources. In addition, having an in-house MSSP unburdens your internal teams, giving them the space to work on other priorities.
Disadvantages of Customizing PCI 4.0:
-
High upfront costs: While many organizations can save money over the long-run, implementing a customized PCI compliance approach involves significant upfront costs. Customization will require specialized expertise from a PCI QSA, additional tools and resources, and potentially the development or integration of bespoke solutions.
-
Requires extensive expertise: More room to customize means more ambiguity on what passes / fails. The absence of standardized benchmarks can make it difficult to assess the effectiveness and consistency of security controls. To navigate the complexities of customizing an organization's compliance approach effectively, it is crucial to have teams with a deep understanding of compliance requirements, security best practices, and emerging threats.
Considerations for Healthcare Organizations: Should you Customize PCI 4.0?
Just because you can customize PCI 4.0, does not mean you should. PCI 4.0 customization is not necessarily for every healthcare organization, especially for those organizations that do not process a large volume of transactions or have complex cybersecurity needs.
When considering whether to adopt a customized approach to PCI 4.0, it is crucial to take into account the specific merchant level your organization falls under.
The Payment Card Industry has established 4 Merchant Levels based on the number of annual transactions a merchant processes:
-
Level 1: Merchants that process over 6 million Visa or Mastercard transactions annually. Alternatively, merchants that have experienced a data breach may be reclassified as Level 1.
-
Level 2: Merchants that process between 1 and 6 million Visa or Mastercard transactions annually.
-
Level 3: Merchants that process between 20,000 and 1 million Visa or Mastercard e-commerce transactions annually.
-
Level 4: Merchants that process fewer than 20,000 Visa or Mastercard e-commerce transactions annually, and all other merchants processing up to 1 million Visa or Mastercard transactions annually.
For Level 1 healthcare organizations looking to advance to next-gen security technology, an MSSP such as Avertium can help design and implement a customized approach to PCI 4.0 to ensure compliance and security. Avertium’s QSAs have the expertise to guide your business through the PCI compliance process.
While Level 2 healthcare organizations, whether or not you should customize PCI 4.0 really depends on two factors:
- How big is your company / what is your growth trajectory?
- How many transactions is your company doing?
If your organization is expecting a significant spike in transaction volume within the next 2-3 years, a readiness assessment done by a PCI QSA can prepare you for the move up to level 1. Ultimately, this reduces a lot of headaches later on by enabling you to be more proactive.
For healthcare organizations that fall under PCI’s merchant Levels 3 or 4, a customized approach to PCI 4.0 is likely not a fit. Instead, opt for a PCI DSS Self-Assessment Questionnaire (SAQ).
Also note that if you are a Level 1 Merchant or Service Provider with a high-volume of transactions, you are not eligible to self-assess your compliance to obtain PCI certification. Instead, you must retain a Qualified Security Assessor (QSA) company.
Finding the Right Partner:
Enlisting a partner is likely the most viable option for healthcare organizations who are interested in customizing PCI controls AND whose merchant classification is either level 1 or 2. But, as always, not all partners are created equal. So how do you know which partner is right for you?
The WRONG partner…
-
Fails to account for your unique business needs: A one-size-fits-all, check-the-box approach may not effectively address the unique security needs of your organization and can overlook specific risks and vulnerabilities that are critical to your organization's operations.
- Fails to be proactive: Merely checking off compliance checkboxes does not guarantee robust security. A checkbox mentality promotes a reactive rather than a proactive approach to security. Instead of continually assessing and managing risks, your organization may prioritize meeting specific requirements without actively identifying and addressing potential vulnerabilities. This reactive approach can leave your organization ill-prepared to handle emerging threats.
The RIGHT partner…
- Tailors their approach to your environment: This begins with a readiness assessment to truly understand your unique environment. This partner should give you an overview of the controls they will want to customize, asking questions such as:
- What is the hardest requirement for your organization to comply with?
- Which one feels like a fire drill?
- Which controls have created the most stress / drive you to be late?
- What do you typically do with the results?
-
Explains the implications of how each custom control impacts testing procedures and other compliance frameworks: The right partner will have a nuanced understanding of various regulations (HIPAA, CMMC, HITRUST, etc.) and how to apply specific activities like penetration tests and vulnerability scans to multiple regulatory frameworks. This will ensure that your organization does not have to duplicate efforts / spend unnecessary budget just to meet a compliance requirement.
Related Resource: 5 Steps to Recovering from a Failed PCI ROC
What is Next for Your Healthcare Organization?
Now is the time for your healthcare organization to bring on the right partner and begin conducting readiness assessments in preparation for PCI 4.0. Proactive action taken now will ensure your organization has adequate time to identify the processes, technical controls, and documentation, along with other security measures that will need to be updated to comply with PCI 4.0. Then, that leaves the remainder of the year – up until the retirement of PCI 3.2.1 on March 31st, 2024 – as the ideal time to conduct working sessions with a trusted MSSP to discuss your organization’s PCI compliance gaps.
At Avertium, we believe that businesses fare better with PCI compliance requirements when they do not have to scramble right before the annual assessment date.
We see PCI compliance as a driver of security maturity, a way to reduce business risk, safeguard business continuity, and protect your company's reputation in the market. Whether you need help building a PCI program from scratch or just need a utility player to fill in the gaps, Avertium offers end-to-end support at every stage of the PCI compliance journey.
Our seasoned PCI QSAs will provide expert guidance and support to ensure your healthcare organization gets everything needed to build a customized and dynamic PCI program that drives efficiency and enhanced cybersecurity maturity throughout your business.
Contact us to learn more about Managed PCI.
APPENDIX II: DISCLAIMER
This document and its contents do not constitute, and are not a substitute for, legal advice. The outcome of a Security Risk Assessment should be utilized to ensure that diligent measures are taken to lower the risk of potential weaknesses be exploited to compromise data.
Although the Services and this report may provide data that Client can use in its compliance efforts, Client (not Avertium) is ultimately responsible for assessing and meeting Client's own compliance responsibilities. This report does not constitute a guarantee or assurance of Client's compliance with any law, regulation or standard.
ABOUT AVERTIUM
Avertium is a cyber fusion company with a programmatic approach to measurable cyber maturity outcomes. Organizations turn to Avertium for end-to-end cybersecurity solutions that attack the chaos of the cybersecurity landscape with context. By fusing together human expertise and a business-first mindset with the right combination of technology and threat intelligence, Avertium delivers a more comprehensive approach to cybersecurity.
That's why over 1,200 mid-market and enterprise-level organizations across 15 industries turn to Avertium when they want to be more efficient, more effective, and more resilient when waging today's cyber war.
Avertium. Show No Weakness.®