DarkSide Ransomware Overview
TIR-20210307 Overview
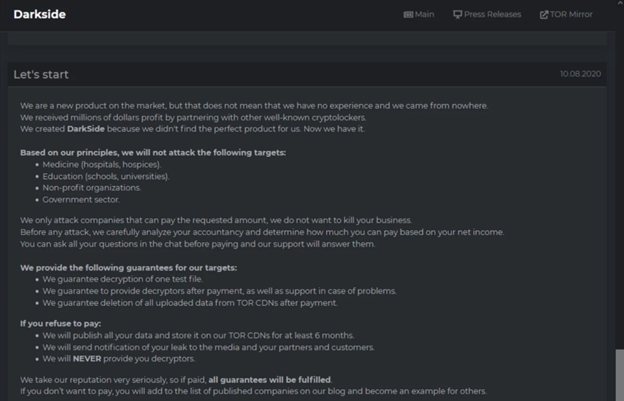
This report is an overview of DarkSide Ransomware, a Ransomware-as-a-Service (RaaS) which primarily targets Windows systems but also has the ability to target Linux OS variants. Formerly known for using the handle 'darksupp', a Russian-speaking cybercriminal posted several announcements regarding DarkSide including an official recruitment for affiliates to participate in the DarkSide RaaS affiliate program. Consequently, those who participate, pledge not to attack hospitals, schools, nonprofits, or government targets and to only attack businesses who can afford to pay a ransom. The operators guarantee test file decryption, support during the decryption process, and deletion of all data upon payment. They also warn that if the ransom is not paid, they will publish the encrypted data for a period of 6 months. In short, this report details the tactics, techniques, and procedures (TTPs), which may vary amongst operators and mitigation techniques that can be implemented to help protect against DarkSide Ransomware.
Related Reading: The Rise of RaaS Gangs + What You Need to Know
DarkSide Ransomware Tactics, Techniques, and Procedures
On August 8, 2020, the operators of DarkSide initially announced their malware in a press release on the dark web, and in November, ‘darksupp’ announced the launch of a recruitment effort for affiliates.
Since the initial announcement, various DarkSide attacks have been investigated and the following statistics have been documented:
Targeted Sectors of Clients: Professional Services and Manufacturing
- Average Ransom Demand: US $6,527,402.02
- Average business downtime: 5 days
- Data exfiltration observed in 100 percent of cases
Procedures in Phases
To begin with, the attack starts with the reconnaissance phase, in which the attacker makes use of MetaSploit and other Offensive Security Tool (OST) frameworks to locate vulnerabilities in the victim’s network with the goal of establishing initial access into the environment. From here, the investigations show the attackers start to move throughout the environment by obtaining access to privileged accounts such as an Administrator RDP sessions on a Domain Controller or by accessing another privileged account to access a file server, etc.
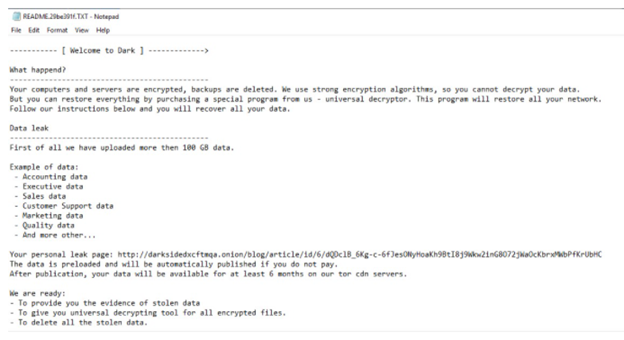
Once the attacker gains privileged access, they begin harvesting data from the victim’s server before encrypting it. In addition, the operators of DarkSide ransomware have established a content delivery network (CDN) used to store and deliver compromised data exfiltrated from victims. Once the data is exfiltrated, it is uploaded to servers in their CDN which are used as an extortion tool for the threat group.
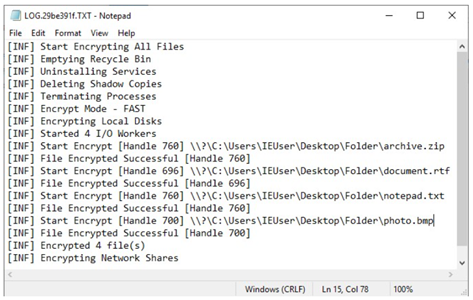
Then, after the data has been stolen, DarkSide creates a log file named ‘LOG.{userid}.TXT’, where it writes the step-by-step ransomware’s execution process. As a result, this file includes the encryption of files, the deletion of Shadow Volume Copies on the system, termination of various processes, etc.
Consequently, after the files have been encrypted, DarkSide leaves the ransom note as ‘README.{userid}.TXT’ file. In particular, DarkSide customizes the ransomware executable for each company they attack charging different ransoms based on the size of the company, the number of devices encrypted, and the amount of data stolen.
Business Unit Impact of DarkSide Ransomware
- Not only can attackers encrypt data on the victim’s system, but also on large numbers of systems in a network to interrupt the availability of system and network resources.
- Additionally, data and sensitive information may be lost, destroyed, or released to the public.
Our Recommendations
- Ensure anti-virus software and associated files are up to date.
- Keep applications and operating systems running at the current released patch level.
- Block indicators of compromise from the IOC list at the firewall
- Ensure users are only downloading software from legitimate vendors.
- Implement an email security solution to detect ransomware and protect against known and unknown threats.
- Not only ensure backups are stored off system, but also ensure that they are protected from common methods adversaries may use to gain access and destroy the backups to prevent recovery.
- Additionally, implement multifactor authentication (MFA).
- Use Group Policy Software Restriction Policies (SRP) to prevent users from executing Windows executable filetypes (e.g., .exe, .dll, .hta, .bat, .scr) from the \AppData\Local\Temp\ path of Office365, Microsoft Word, Excel, and Outlook.
Sources
IOC List
- Visit the following sites for a list of file names, hashes, and domains associated with this attack:
- https://www.areteir.com/darkside-ransomware-caviar-taste-on-your-big-game-budget
- https://www.acronis.com/en-us/articles/darkside-ransomware/
- https://www.digitalshadows.com/blog-and-research/darkside-the-new-ransomware-group-behind-highly-targeted-attacks/
- https://exchange.xforce.ibmcloud.com/collection/Darkside-Ransomware-Targeting-Large-Businesses-d0c7cc6f0b2289c23581ca363510a6bc
DarkSide Ransomware Supporting Documentation: MITRE Mapping(s)
- https://attack.mitre.org/techniques/T1082/
- https://attack.mitre.org/techniques/T1057/
- https://attack.mitre.org/techniques/T1078/
- https://attack.mitre.org/techniques/T1098/
- https://attack.mitre.org/techniques/T1059/001/
- https://attack.mitre.org/techniques/T1569/
- https://attack.mitre.org/techniques/T1087/
- https://attack.mitre.org/techniques/T1222/
- https://attack.mitre.org/techniques/T1486/
- https://attack.mitre.org/techniques/T1490/
- https://attack.mitre.org/techniques/T1569/002/
- https://attack.mitre.org/tactics/TA0010/
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.