Malware Campaign utilizes Microsoft Executable MSBuild
Overview of TIR-20210516
This report is about a malware campaign using a well-known Microsoft executable called MSBuild to propagate in a file-less manner. The type of malicious software being used is remote access tools (RATs) and information stealers. This kind of attack uses a living off the land binary (LOLBin) strategy while operating completely in memory.
Tactics, Techniques, and Procedures
The bad actor behind the campaign uses the legitimate Microsoft operating system executable MSBuild to create .proj files on the affected device. The project files will be used to load into memory the process for creating a desktop shortcut, loading malicious software into memory, or for loading shellcode into memory. If the shellcode option is utilized, then a callback function is created allowing for any processes launched by MSBuild to have malicious code injected into it. The attack flow can be seen in more detail below:
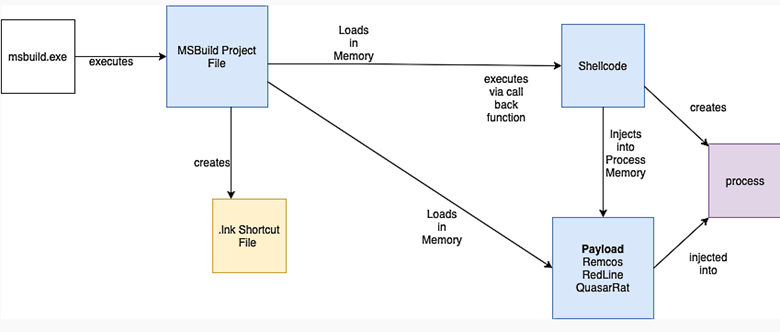
The tooling used by the threat actor includes some common malware used to collect sensitive information on the target. The first tool being deployed is RemcosRAT which is deployed via the project files created from MSBuild. RemcosRAT is a legitimate commercially designed application used for remote access, remote control, penetration testing, and more. Some of the features include anti-virus evasion, credential harvesting, keylogging, the ability to take screenshots, and script execution. The RemcosRAT has been modified to restart anytime the process has been terminated. The second tool associated with this campaign is the RedLine Stealer which is also deployed via project file with a desktop shortcut. The stealer is designed to acquire browser cookies, user credentials for multiple applications including VPNs, financial data such as credit cards, and system configuration data. The final tool used in this campaign is the QuasarRAT which is deployed similarly to the other malicious software. QuasarRAT can perform multiple activities on the affected host including remote shell, remote desktop, keylogging, reverse proxy connections, system modification, and much more!
MSBuild is an executable used to manage and build custom applications in the C++ and .NET programming languages. The executable saves any code prior to the compilation as project files with the extension of .proj. The project files are saved in an XML type format. MSBuild can be used in conjunction with Microsoft Visual Studio or by itself.
TIR-20210516 Business Unit Impact
- May lead to the compromise of sensitive high-value user credentials.
- May result in the loss of highly sensitive financial data such as credit cards, cryptocurrency, and much more!
- Could provide for opportunities to laterally move through the environment with stolen credentials.
Our Recommendations
It is highly encouraged that you implement rules in your SIEM or EDR (Endpoint Detection and Response) tools to monitor MSBuild more carefully. Look out for MSBuild usage on devices where that application should not be running. Consider turning on command line logging for all mission-critical assets such as domain controllers, senior management workstations, Exchange servers, and development environment machines.
Sources
Supporting Documentation
- https://www.anomali.com/blog/threat-actors-use-msbuild-to-deliver-rats-filelessly
- Information on MSBuild
MITRE Mapping(s)
Note: The Avertium Threat Report analyzes one current threat that has been shared by threat intelligence networks across the globe. Used internally by the Avertium CyberOps Team, this report will outline a “top-of-mind” threat and how it ought to be addressed accordingly.
This informed analysis is based on the latest data available.